LinkedIn with Just-in-Time Provisioning
Goal
After completing this setup guide, you will have set up LinkedIn with Just-in-Time Provisioning and your Atlassian product for the SAML SSO for Atlassian Server or Data Center app. Additionally, you will enable the SSO redirection and test SSO.
If you need help, please reach out to us at https://www.resolution.de/go/support. You can also book a free meeting via https://www.resolution.de/go/calendly.
This will allow any LinkedIn user to log in to your instance since this will create an account for them. You cannot limit user access from the Twitter side, but it is possible to block users with SAML SSO. Please contact us at https://www.resolution.de/go/support in that case.
With default settings, these users will not be part of an application access group (see Limitations). When granting users application access, please remember any security implications - any LinkedIn user can use your Atlassian product in this case!
Prerequisites
To use the SAML SSO app for Atlassian Server or Data Center with Azure AD, you need the following:
A LinkedIn Account
A (trial) subscription for the SAML SSO app
Admin access to your Atlassian product
Limitations
By default, the newly created users will not have application access because they are not added to a group during login. This can be changed, please see (6.14.x) JIT Connector: Users do not have application access.
In the context of Jira Service Management, users will be automatically redirected to the service management portal.
Step-by-Step Setup Guide
Install the SAML SSO App
In your Atlassian product, open the in-product marketplace as described in the Atlassian documentation.
Search for "resolution saml" and click "Install" for SAML Single Sign On (SSO) by resolution Reichert Network Solutions GmbH.
After the installation is complete, click Manage Apps/Addons.
Configure SAML SSO
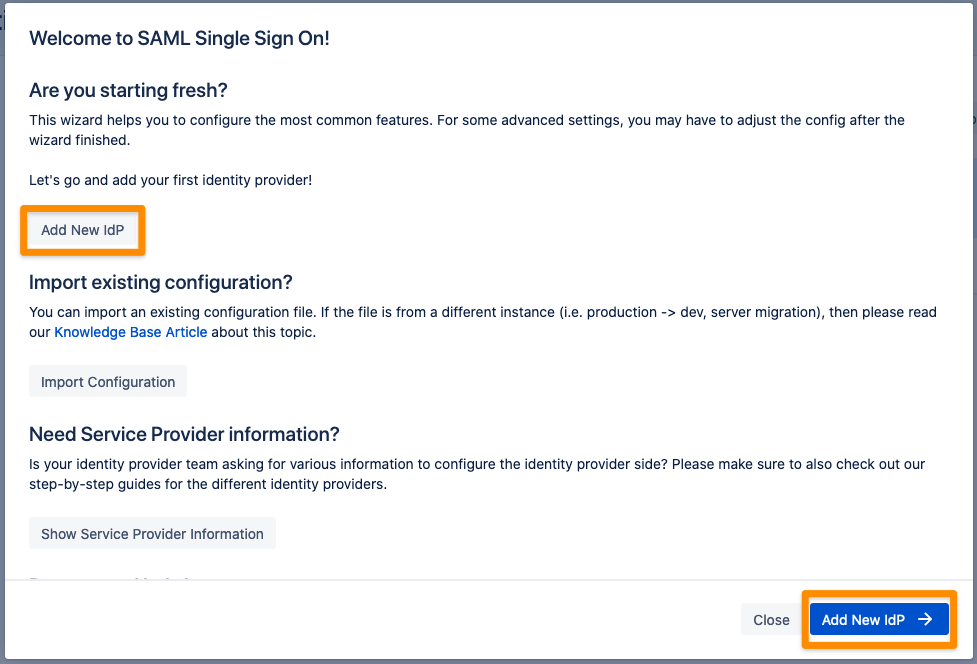
After you clicked "Configure", the Wizard will be triggered. If not, or if you want to add another Identity Prover (IdP) to your existing configuration, click on "+ Add IdP". This guide assumes, that there is no IdP configured.
The Wizard greets you with information, click on "Add new IdP" to proceed.
Choose LinkedIn for your Identity Provider and click Next.
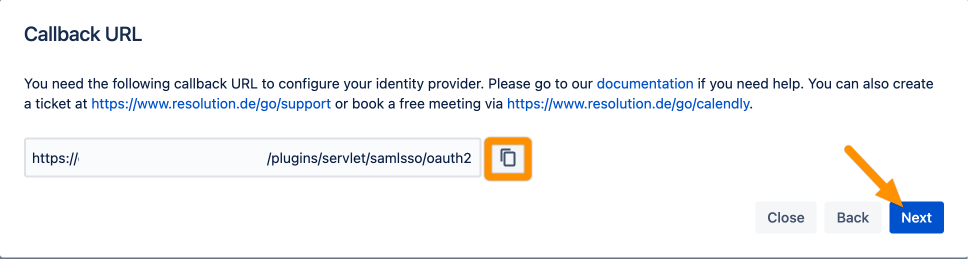
Copy the Callback URL and keep it ready for the next step. Click Next.
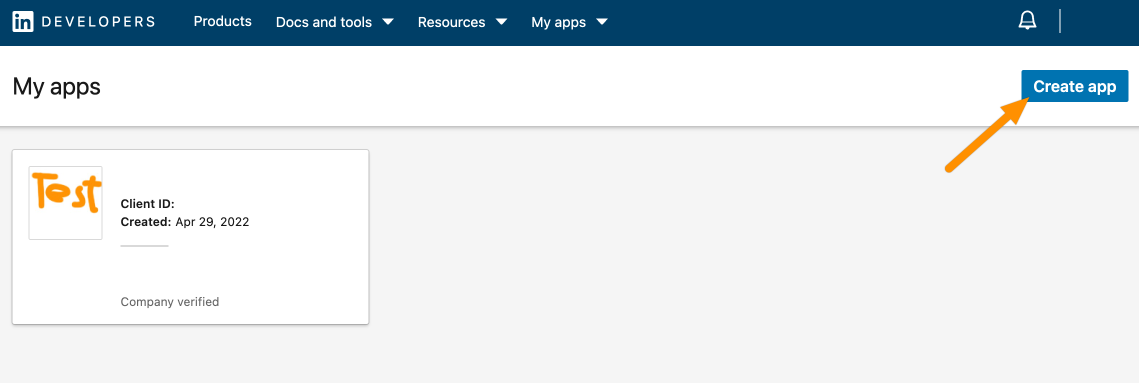
Go to https://www.linkedin.com/developers/apps and log in with your LinkedIn account.
Click Create app.
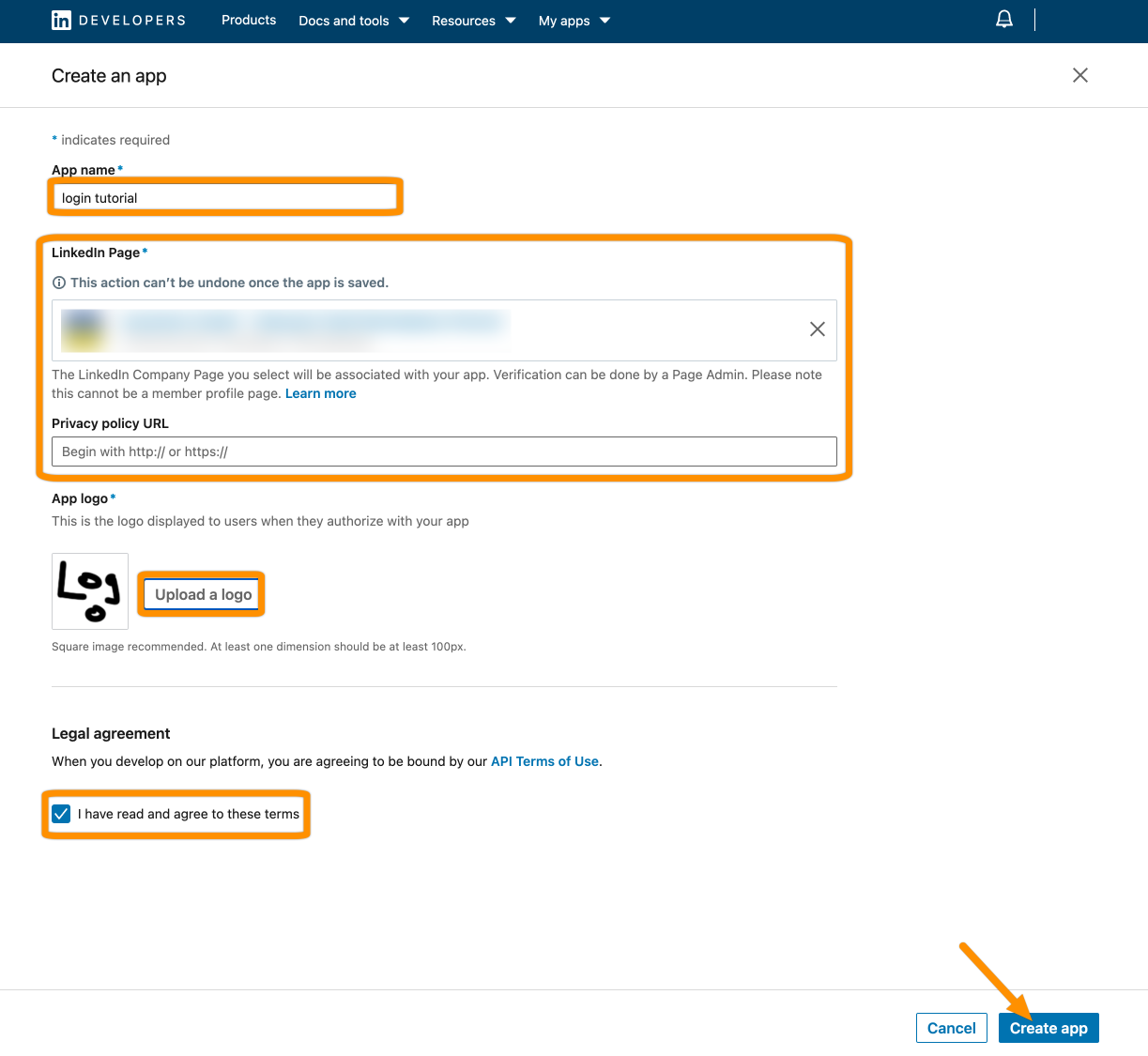
Provide an App name, either link or create a new LinkedIn page, upload a logo and accept the terms. Then click Create app.
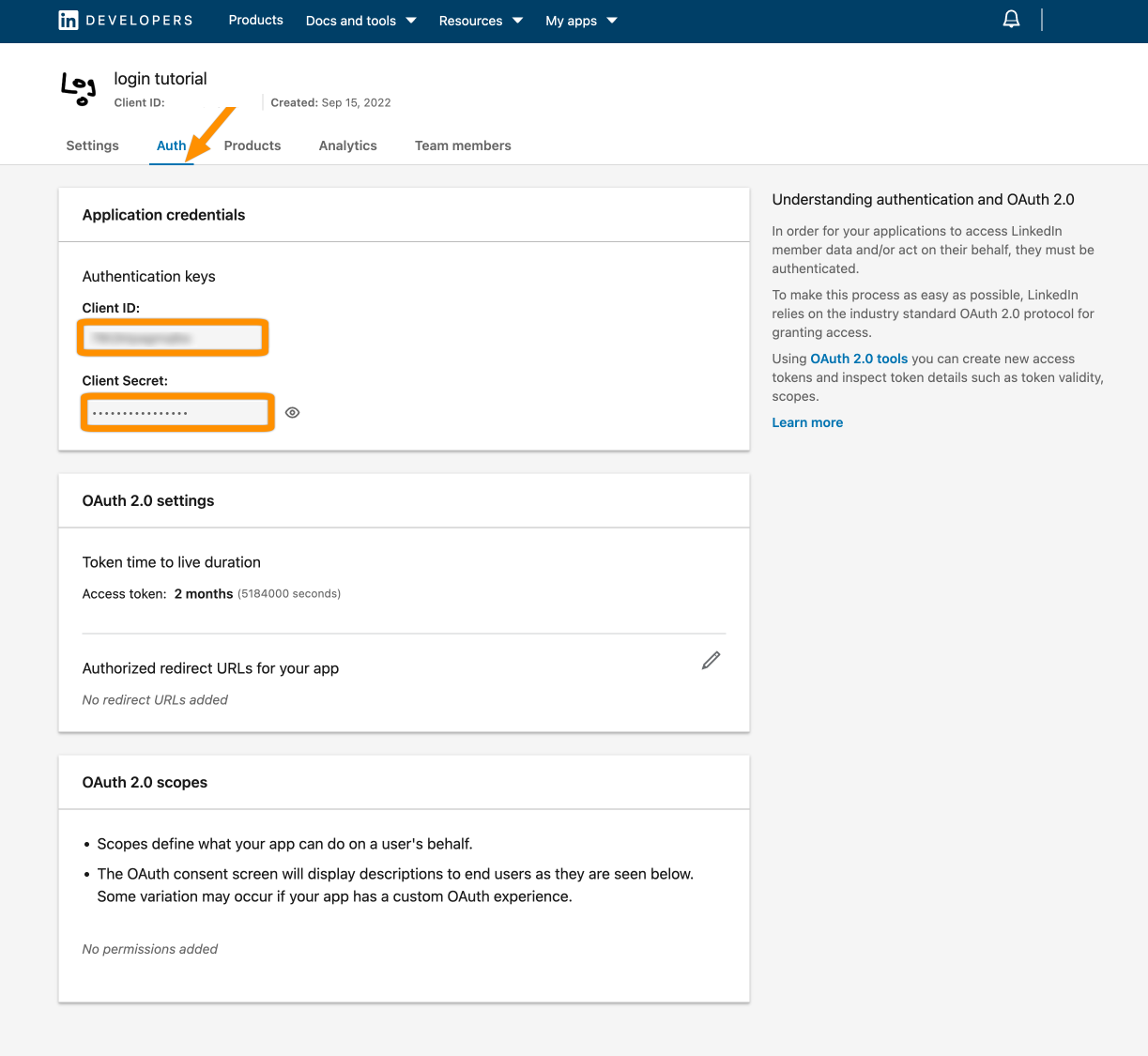
Click Auth from the item bar. Next, copy the Client ID and Client Secret (click the eye button) to your favorite text editor.
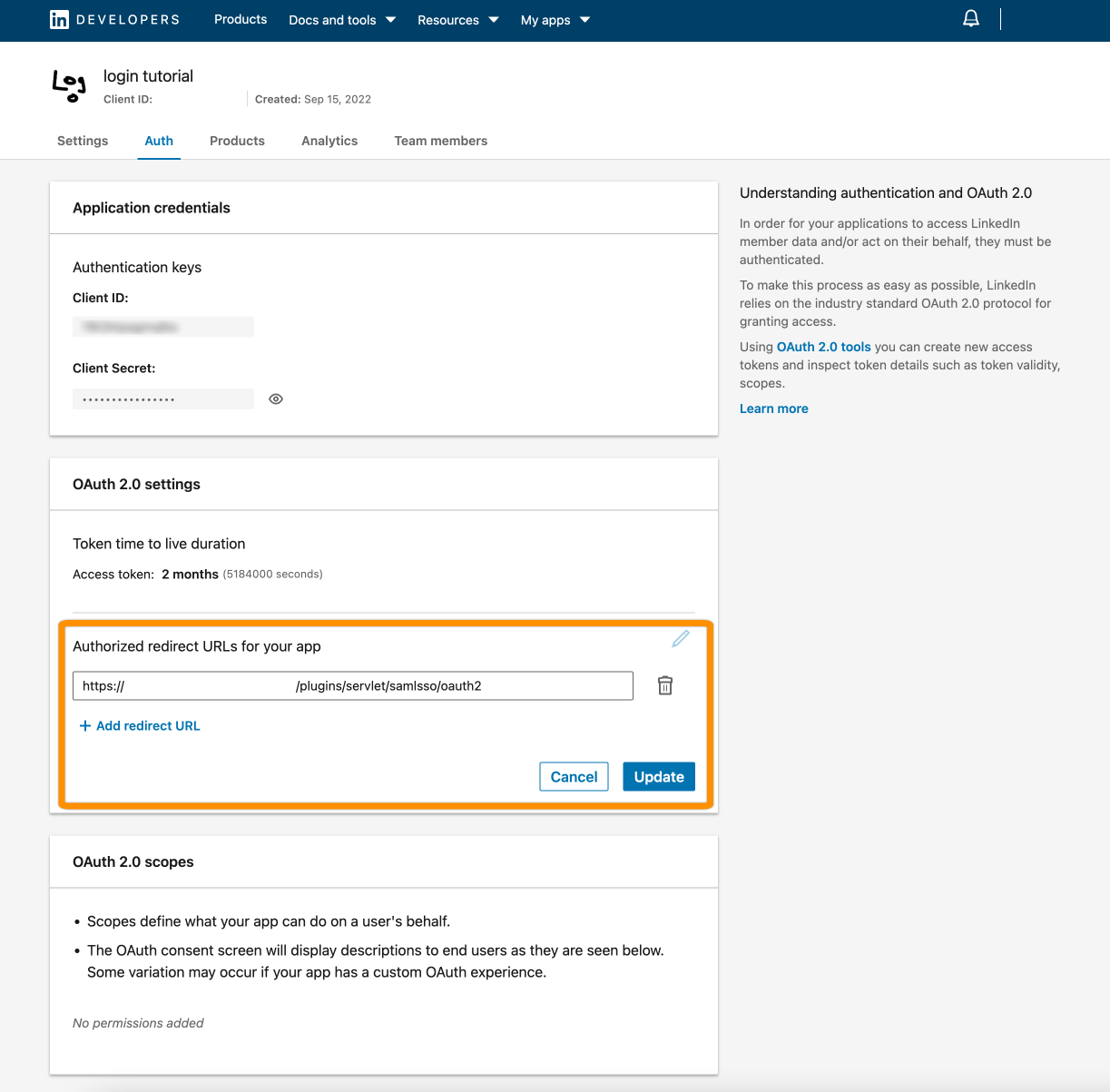
Now, click the pen icon and add the callback URL from the wizard. Hit Update to save this.
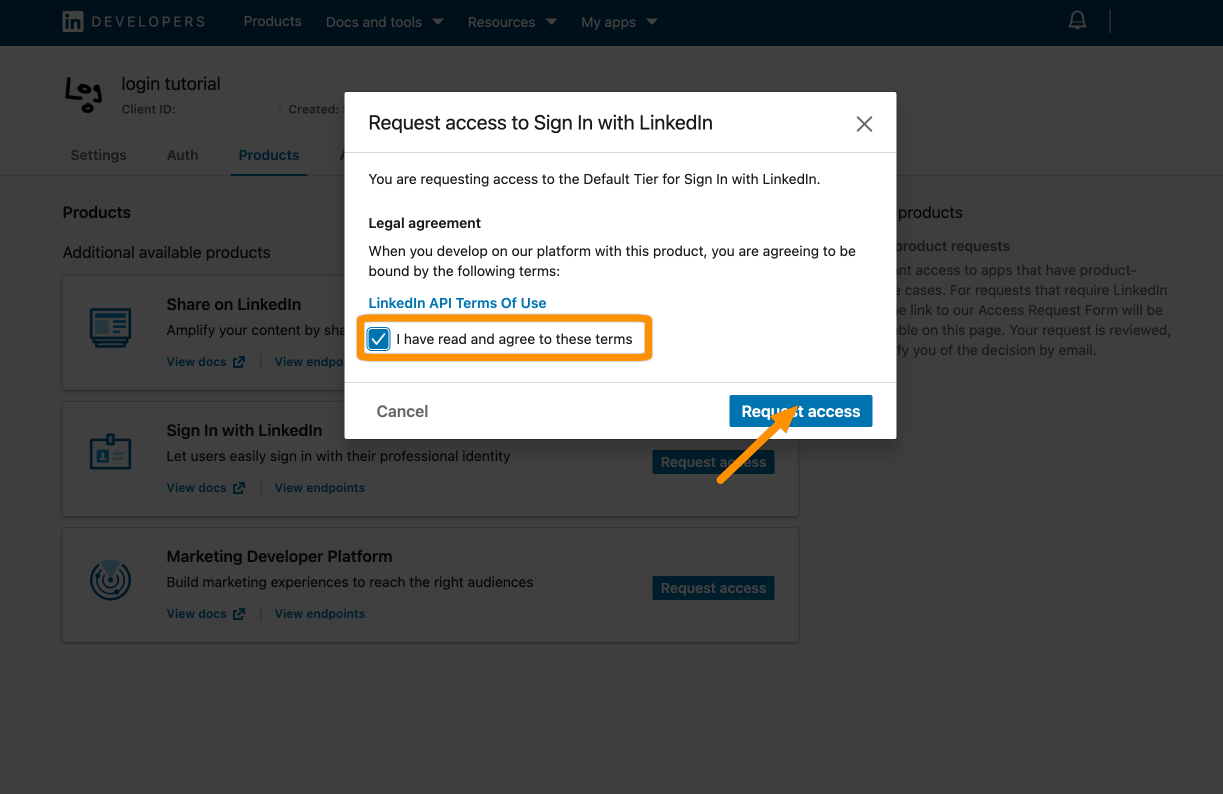
Next, we must activate Sign in with LinkedIn. Click Products and then Request access.
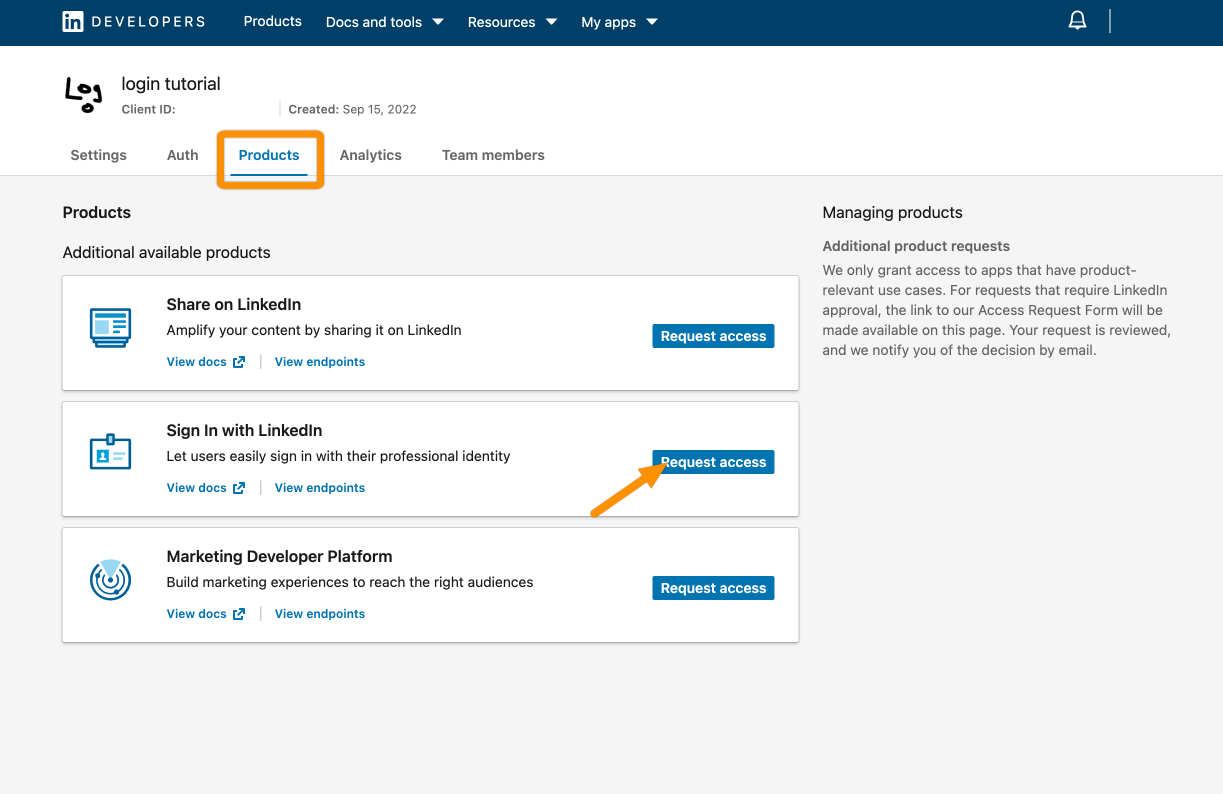
Mark that you "read" the terms and click Request access.
Add the Client ID and Client Secret. Click Done.
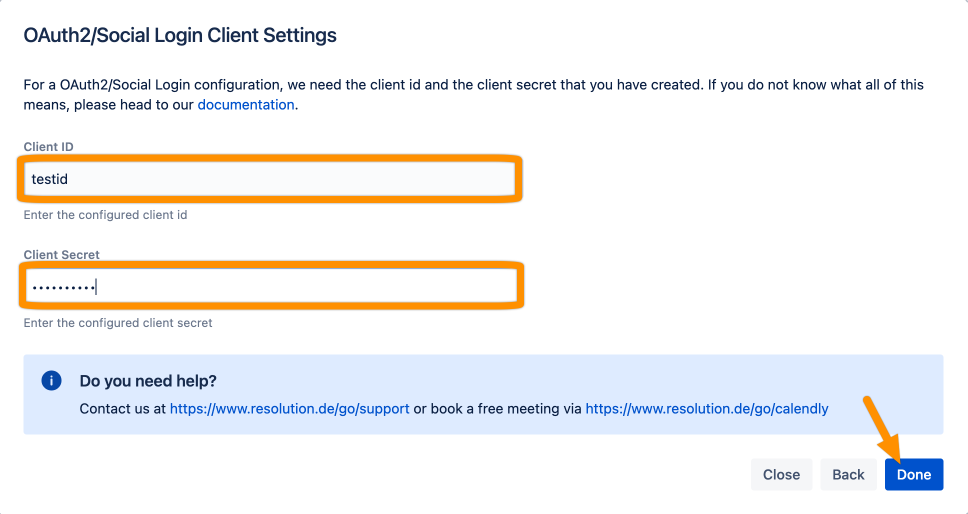
Click Save to save the configuration.
To set up Just-In-Time provisioning, scroll down to User Creation and Update from UserSync-Connector.
Click Create and Setup Just-In-Time Connector.
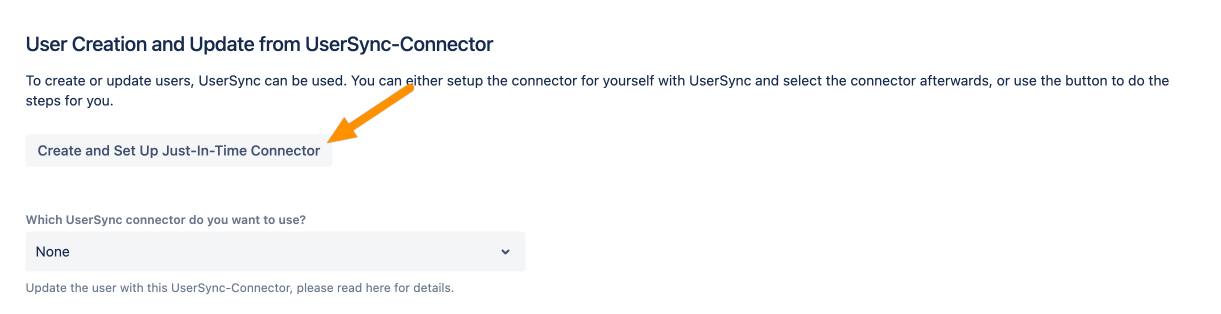
Afterward, Save the configuration to make the change permanent. Now, when a user logs in, the user is created and/or updated.
That's it! When users log in, their accounts will be created and updated during login.
