OpenID Connect for Okta with Manual Provisioning
Goal
Configure SAML Single Sign-On for Atlassian Data Center / Server to work with Okta and manual provisioning, using the OpenID Connect protocol.
Prerequisites
Okta Directory
Your Atlassian Data Center / Server application must be accessible via HTTPS. (read more about it in the Atlassian documentation, i.e. for Jira or Confluence)
Step-by-Step Setup Guide
Find below a detailed guide on how to complete the setup of the SAML Single Sign On app with Okta and manual user provisioning,
meaning that users from Okta have to exist in your Atlassian application already.
If you need any further support, please feel free to contact us here.
Install the SAML SSO app
In your Atlassian product, open the in-product marketplace as described in the Atlassian documentation.
Search for "resolution saml" and click "Install" for SAML Single Sign On (SSO) by resolution Reichert Network Solutions GmbH.
After the installation is complete, click on Manage, then choose Configure.
Now, you are on the Add-on / app configuration page and the first step of the setup wizard will appear.
Configure SAML SSO app
For the next steps, please go to Manage apps (or addons), choose SAML SSO and click Configure.
First Steps - Wizard
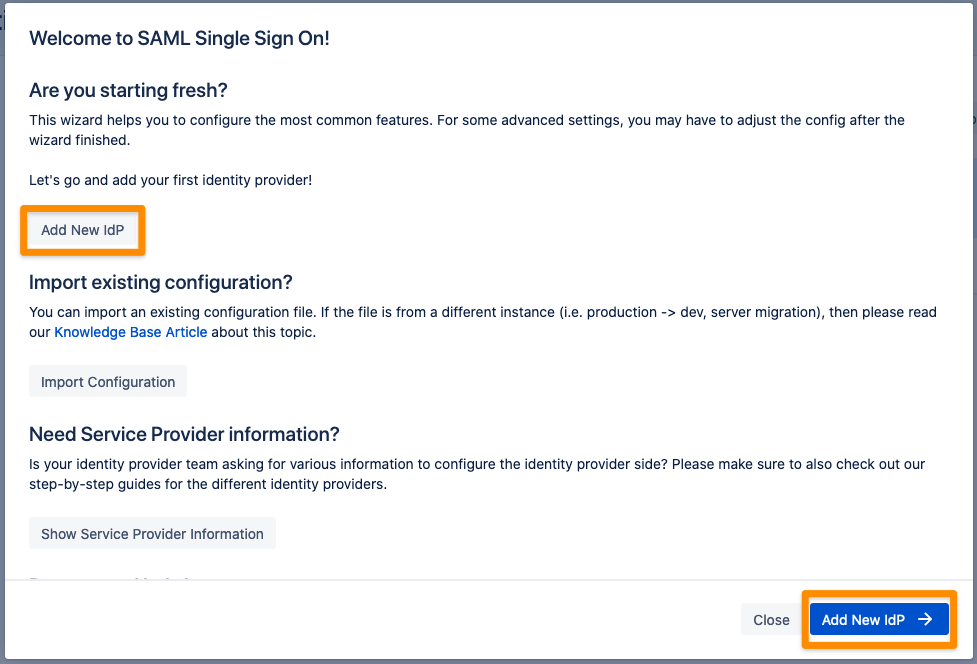
After you clicked "Configure", the Wizard will be triggered. If not, or if you want to add another Identity Prover (IdP) to your existing configuration, click on "+ Add IdP". This guide assumes, that there is no IdP configured.
The Wizard greets you with information, click on "Add new IdP" to proceed.
Select Okta for your identity provider and select OpenID Connect for the authentication protocol. Enter a unique name and click Next to continue. 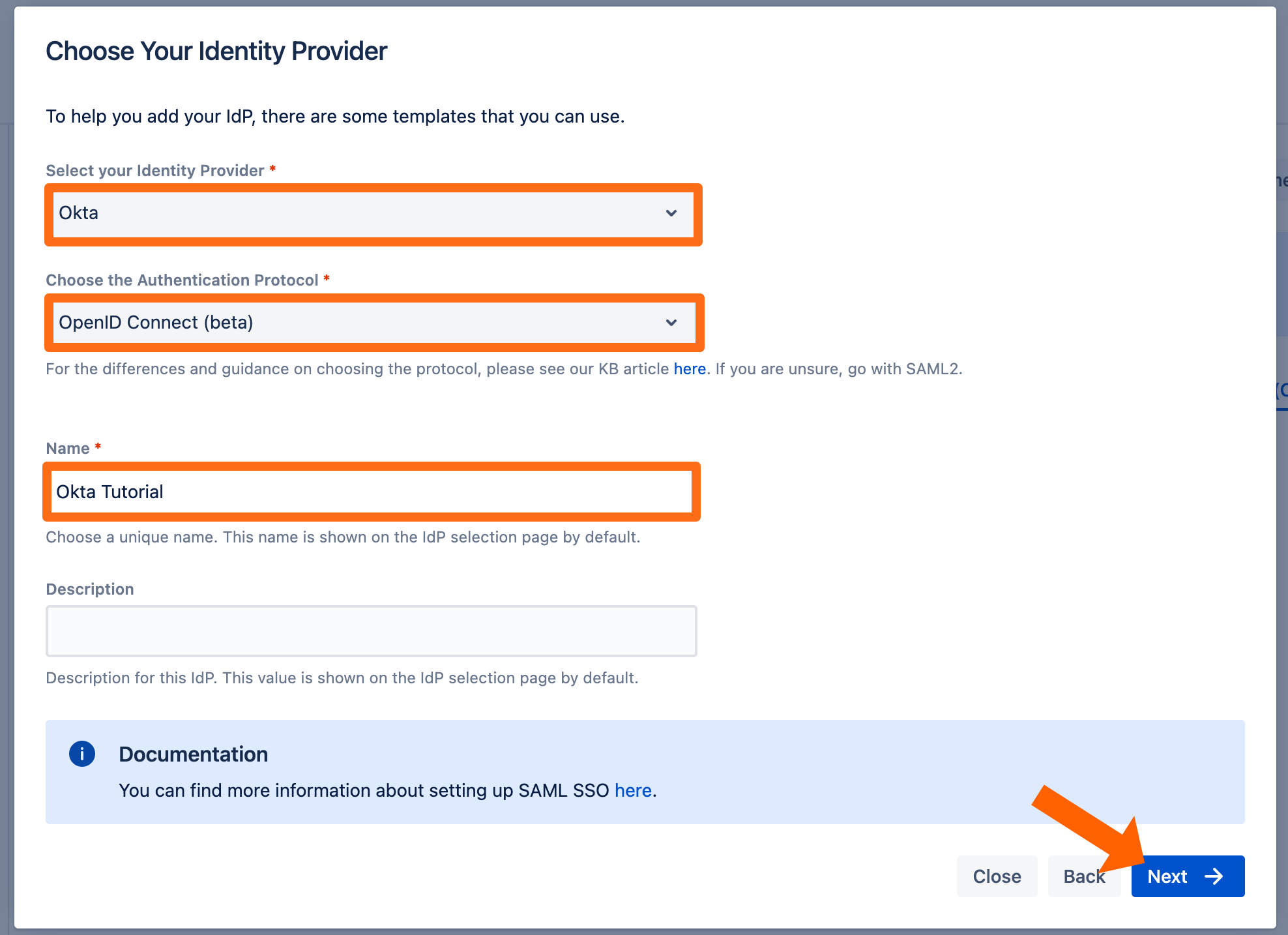
Copy the callback url to your favourite text editor. 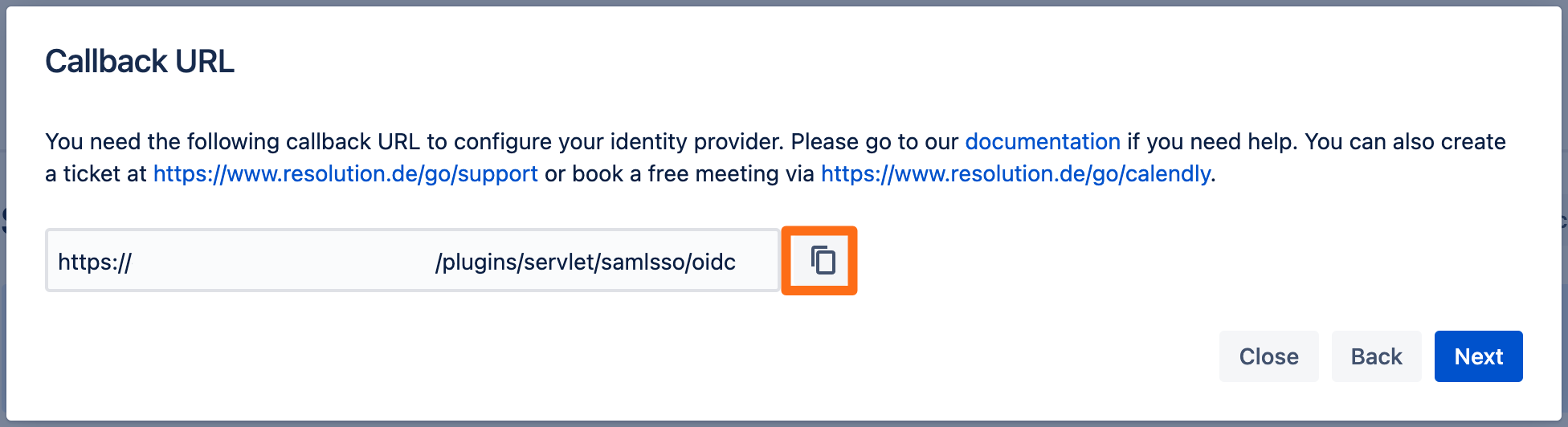
Next go to your Okta site.
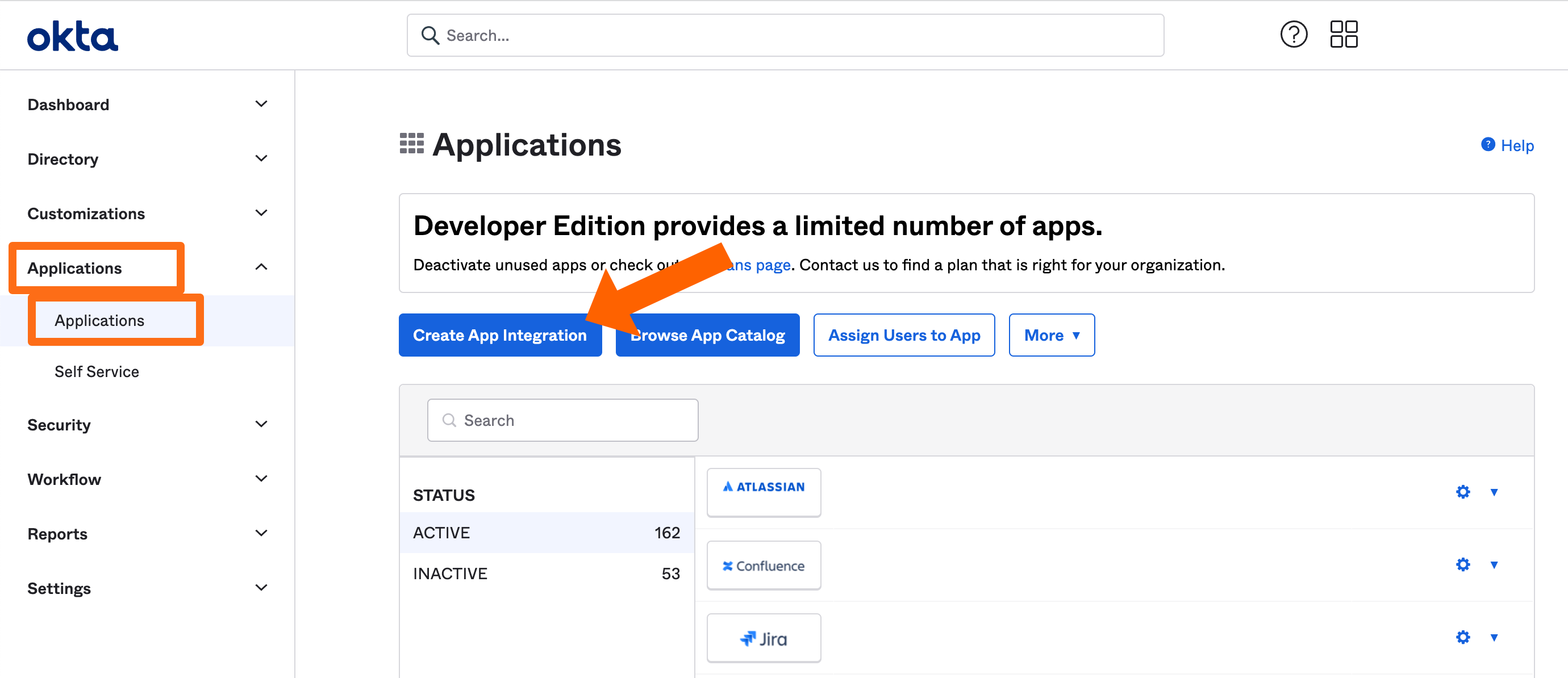
Go to Applications and click Create App Integration.
For the Sign-in method choose OIDC - OpenID Connect and for the Application type choose Web Application. Afterwards continue by selecting Next.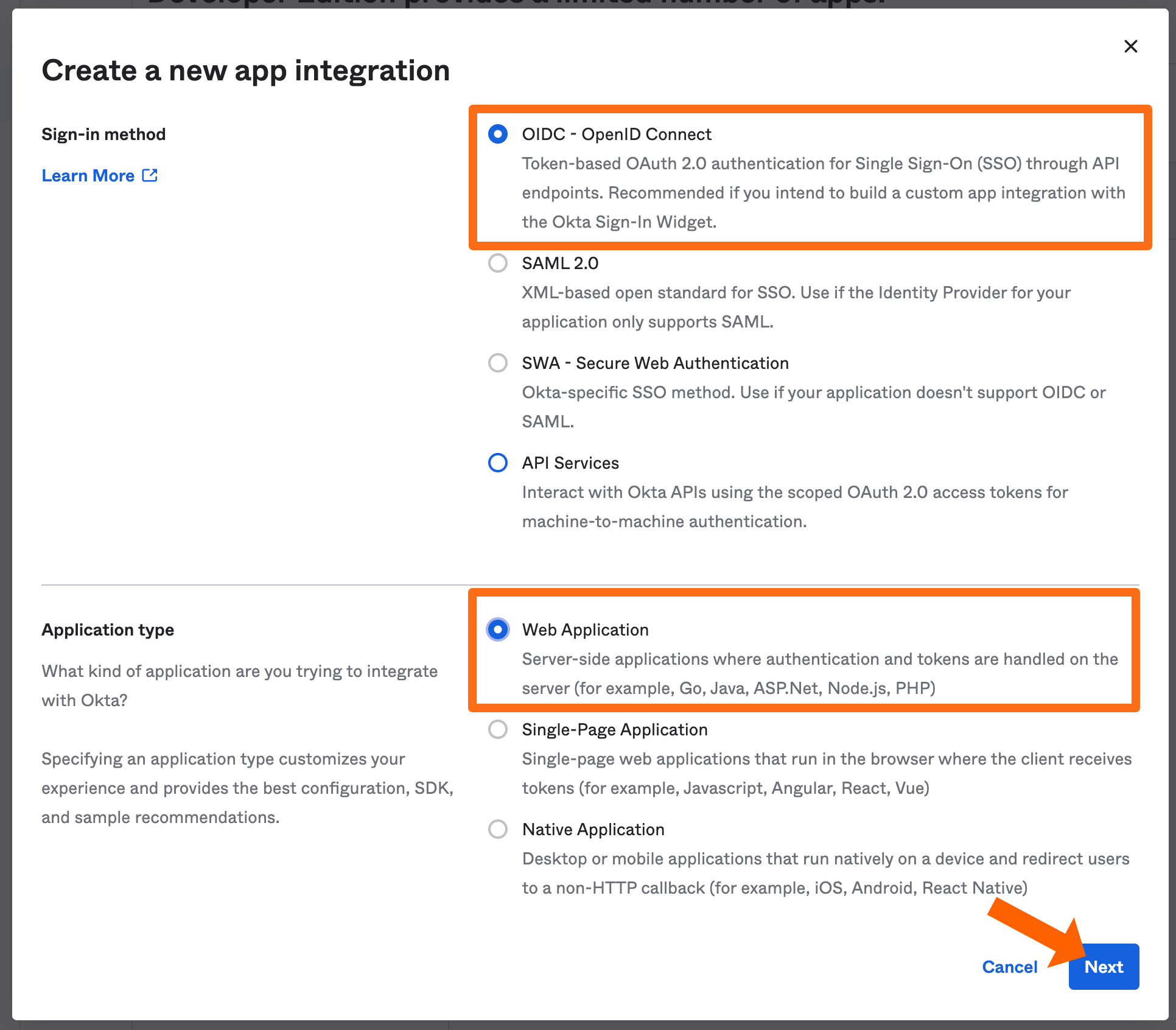
On next page, set an App integration name and paste the callback url to the Sign-in redirect URIs. Additionally, you can delete the Sign-out redirect URI.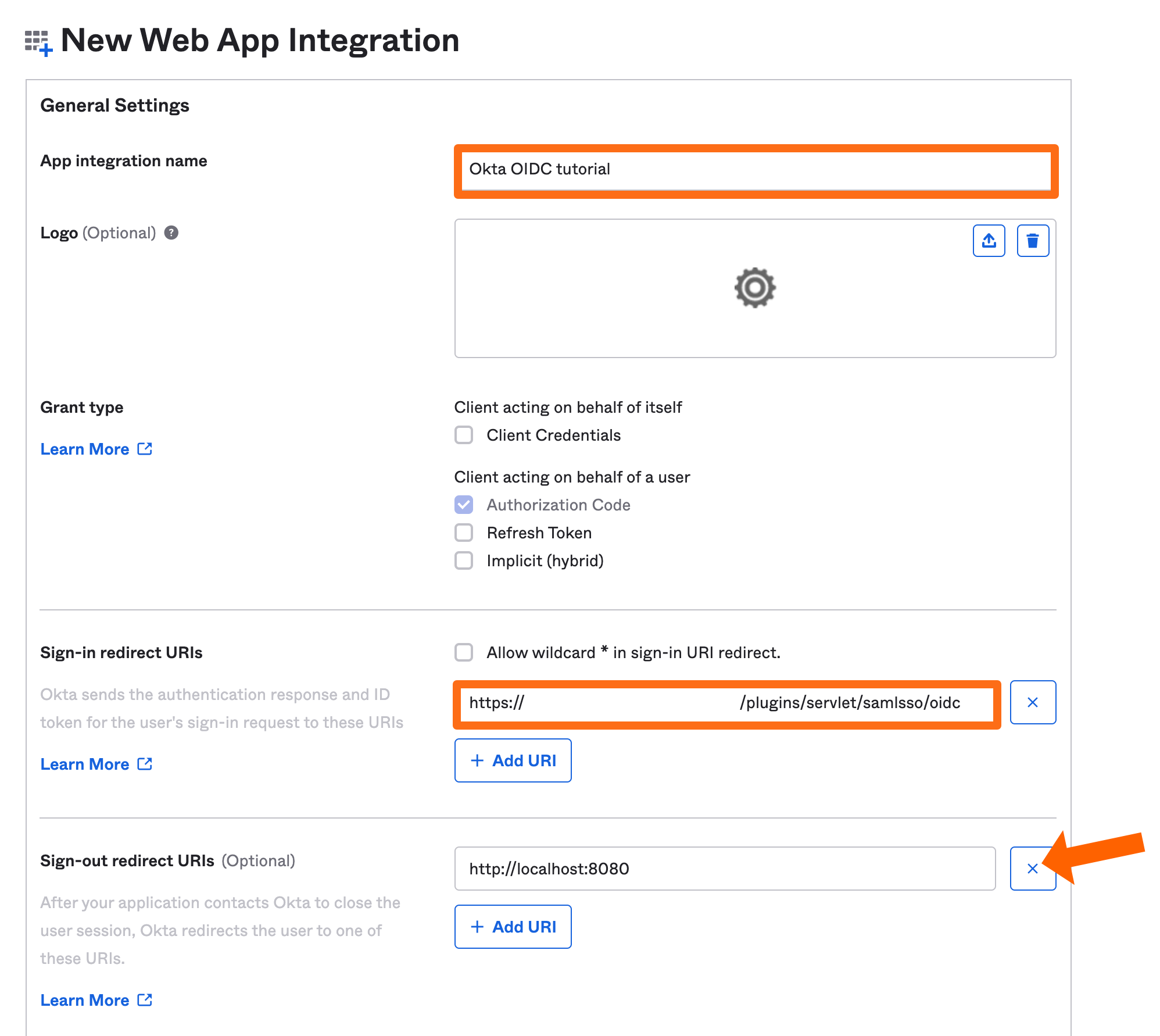
Scroll down to the Assignments section. Here you define who can use this Okta integration to login. E.g., you can allow all users to use it or you can restrict it to certain groups. Select what suits you the best way and click Save to continue.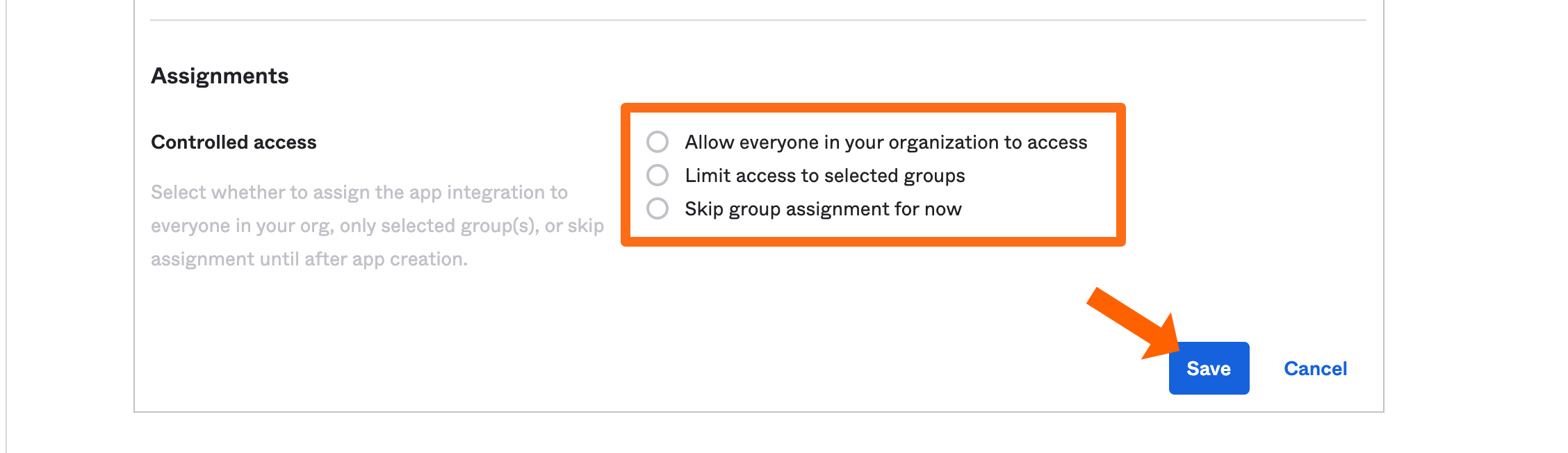
On the next page, please copy the Client ID, Client secret and your Okta domain to a text editor of your choice. We will need those later again.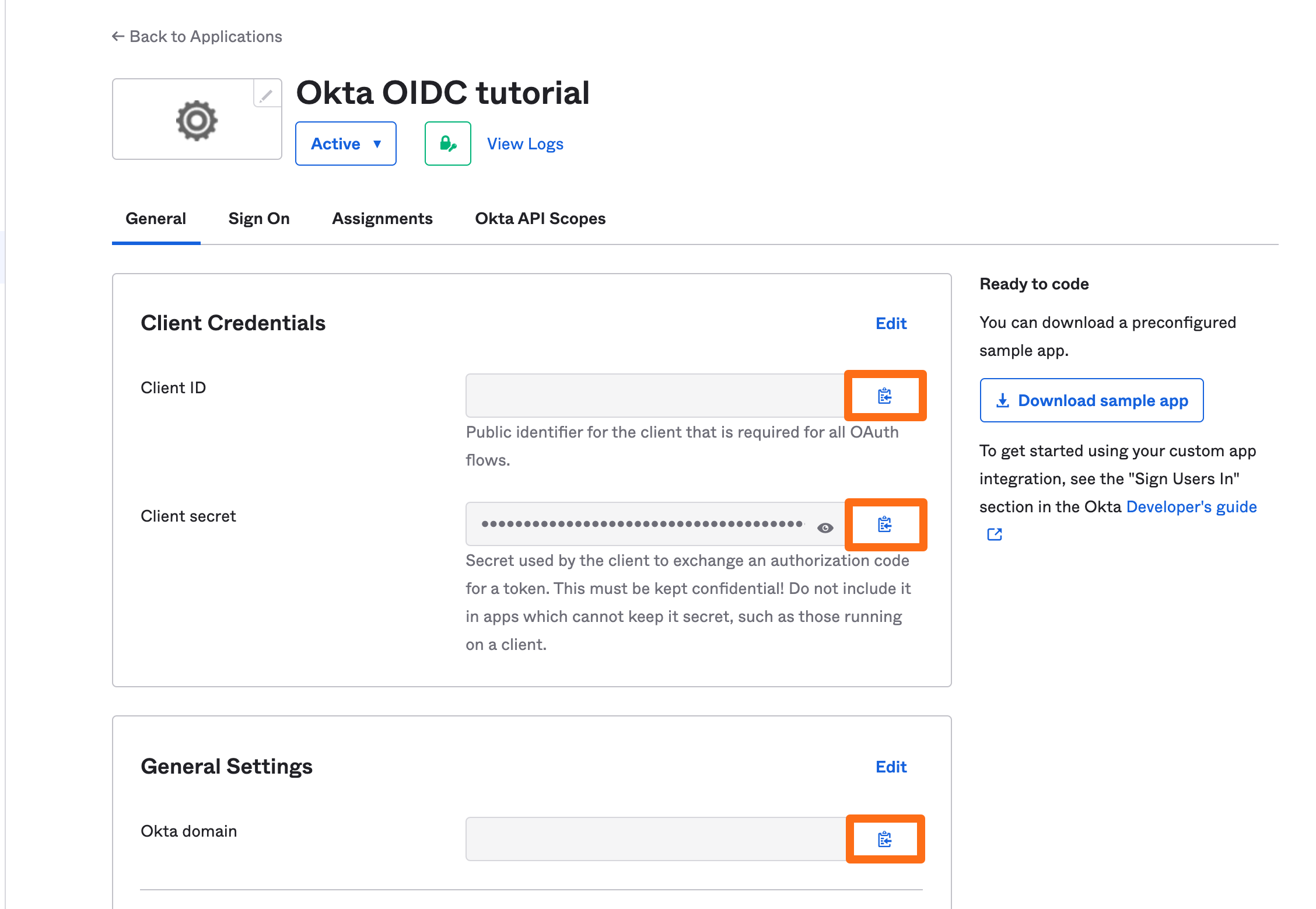
Next, enter your Okta domain from before and click the Import Metadata button.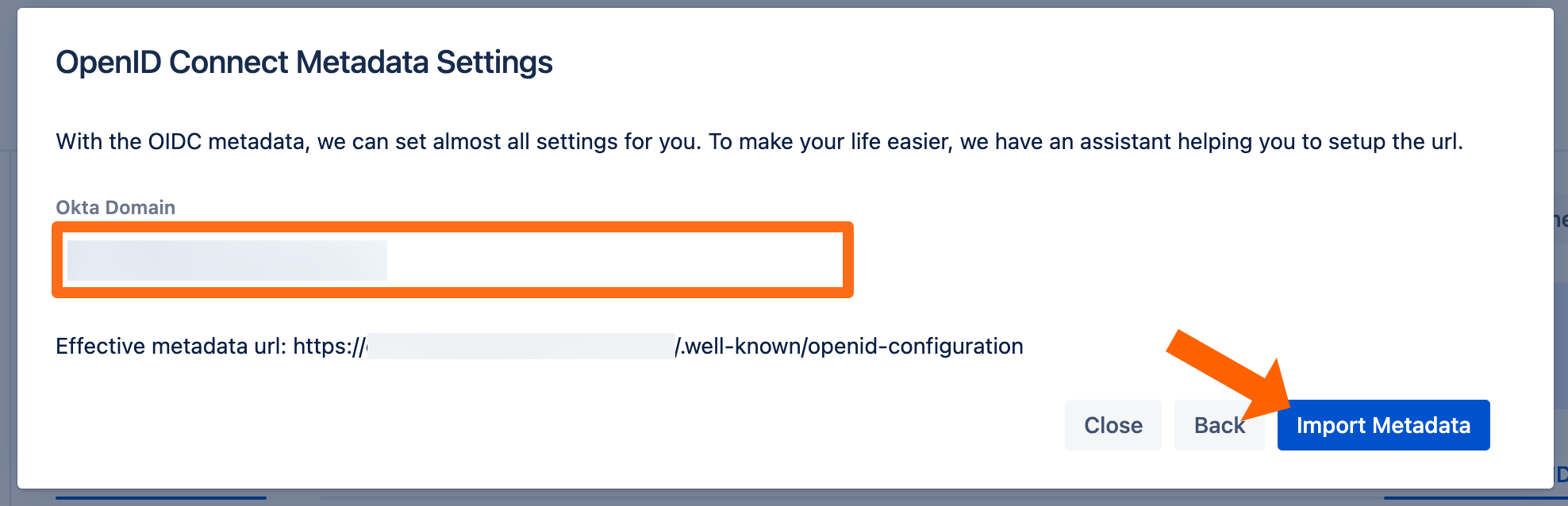
You will see this message if the import was successful.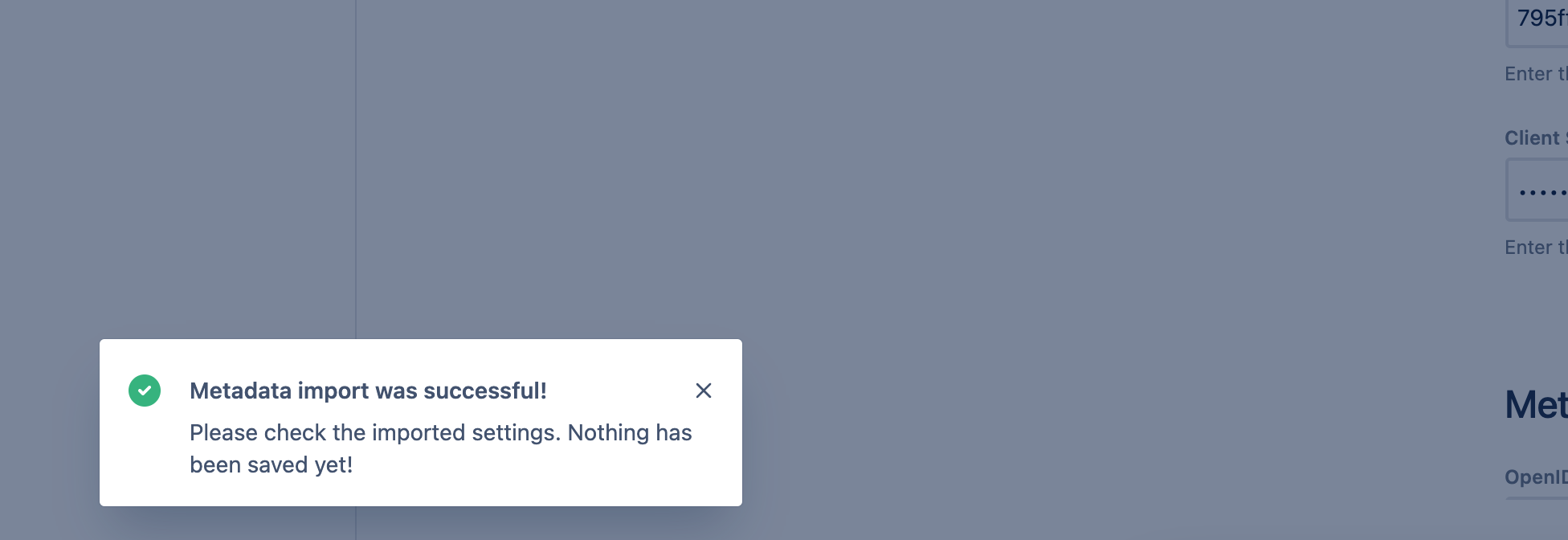
To finish the wizard, click Save and Close.
Testing SSO
To test you configuration, go to the System & Support section of the app and scroll down to the Tracker List.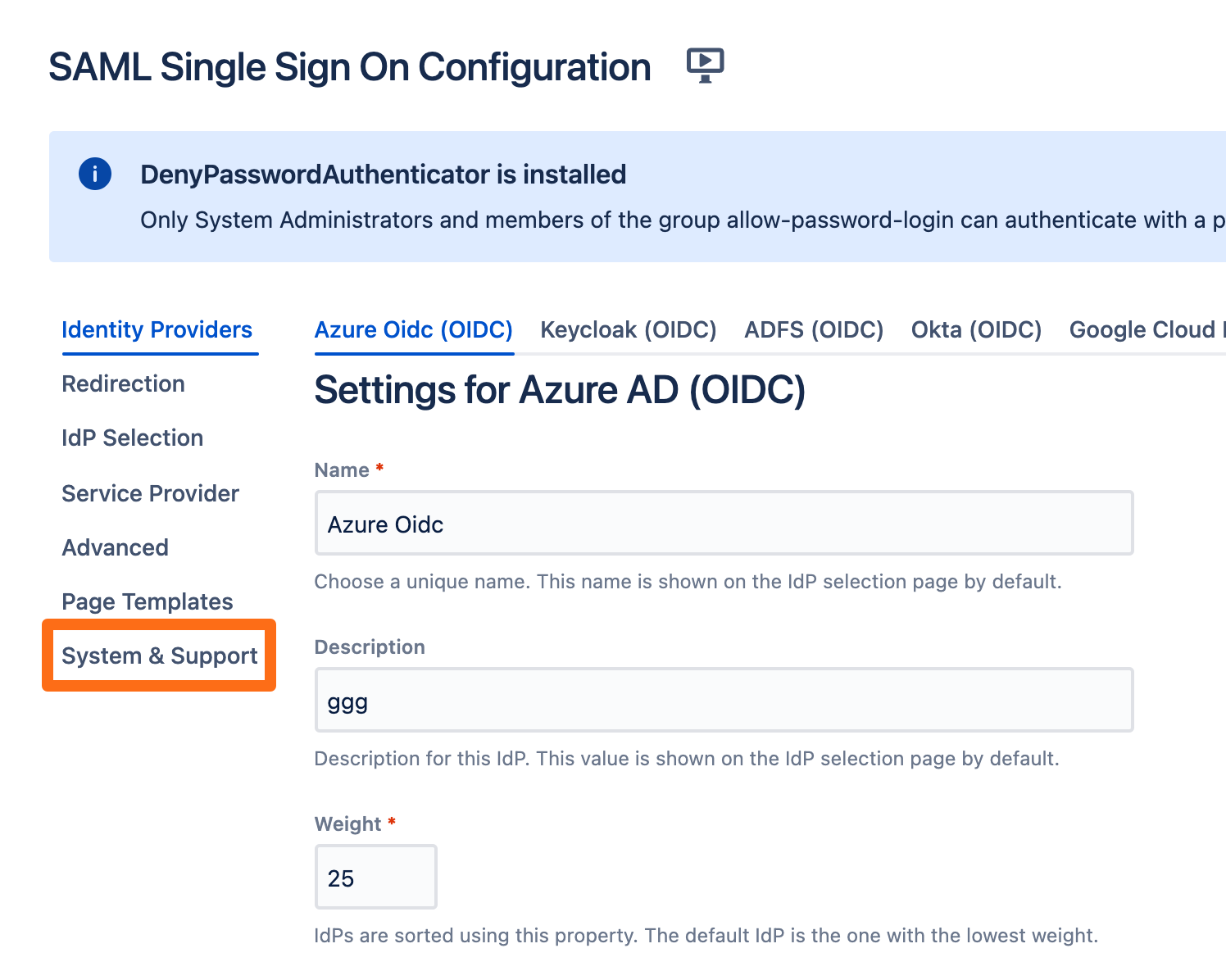
Click New Tracker. If you have more than one identity provider configured, you must choose which configuration should be used for the log in test.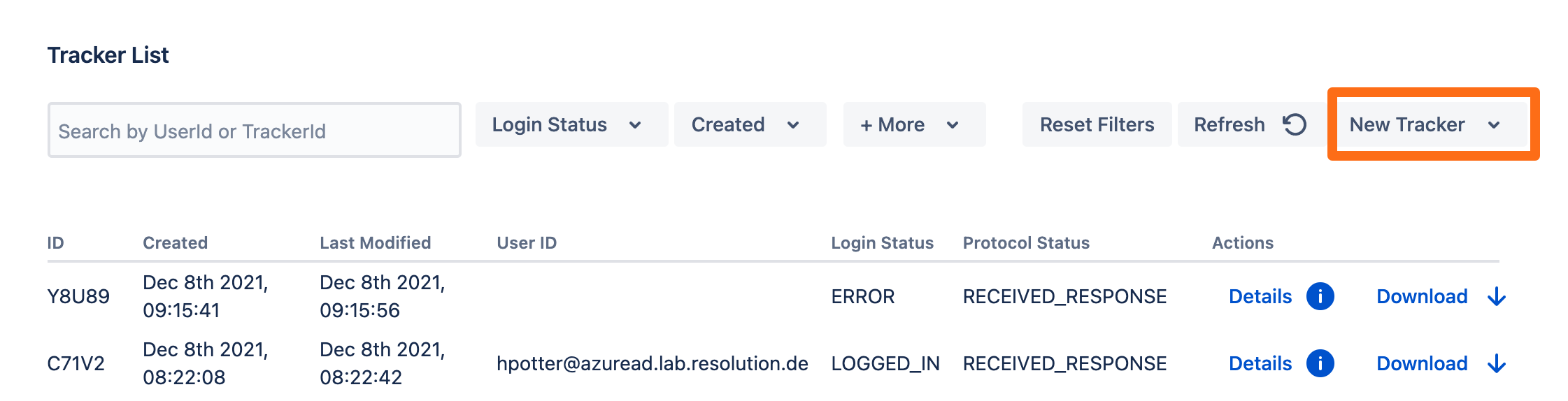
Copy the test url and open the link an incognito web browser. If something goes wrong during the test, you can easily create a support ticket that includes this tracker by click Contact Support. Additionally, you can contact us by going to https://www.resolution.de/go/support or booking a free meeting via https://www.resolution.de/go/calendly.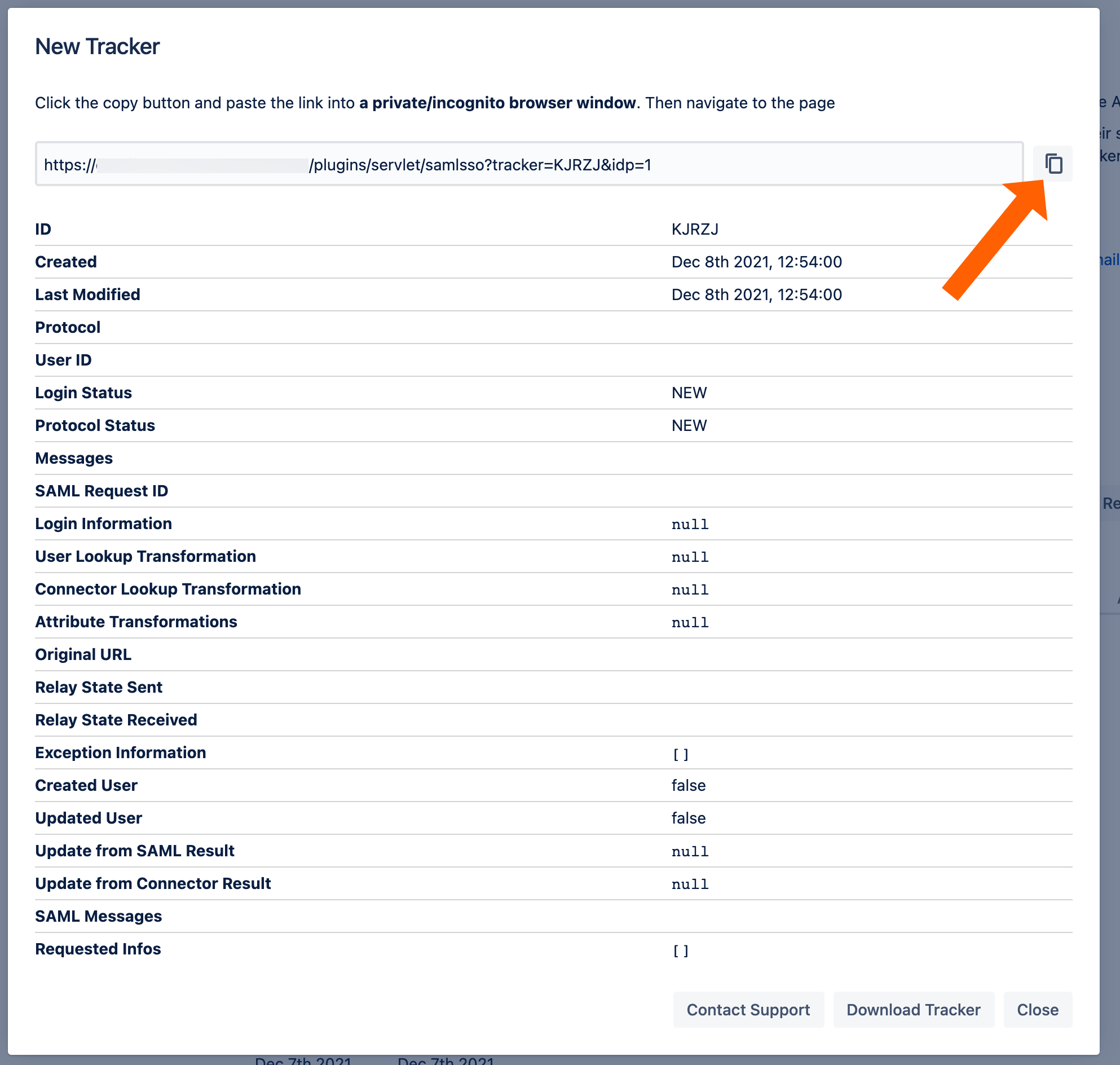
Redirect to SSO
After a successful test, the next step is to configure the redirection. With the redirection setting, the app can automatically redirect users to log in via OpenID Connect.
Go change this setting, go to Redirection from the middle panel.
By checking Enable SSO Redirect, users will get redirected to the configured SSO provider for login. If you are running JSM, you find a second option below.
Click Save to finish the configuration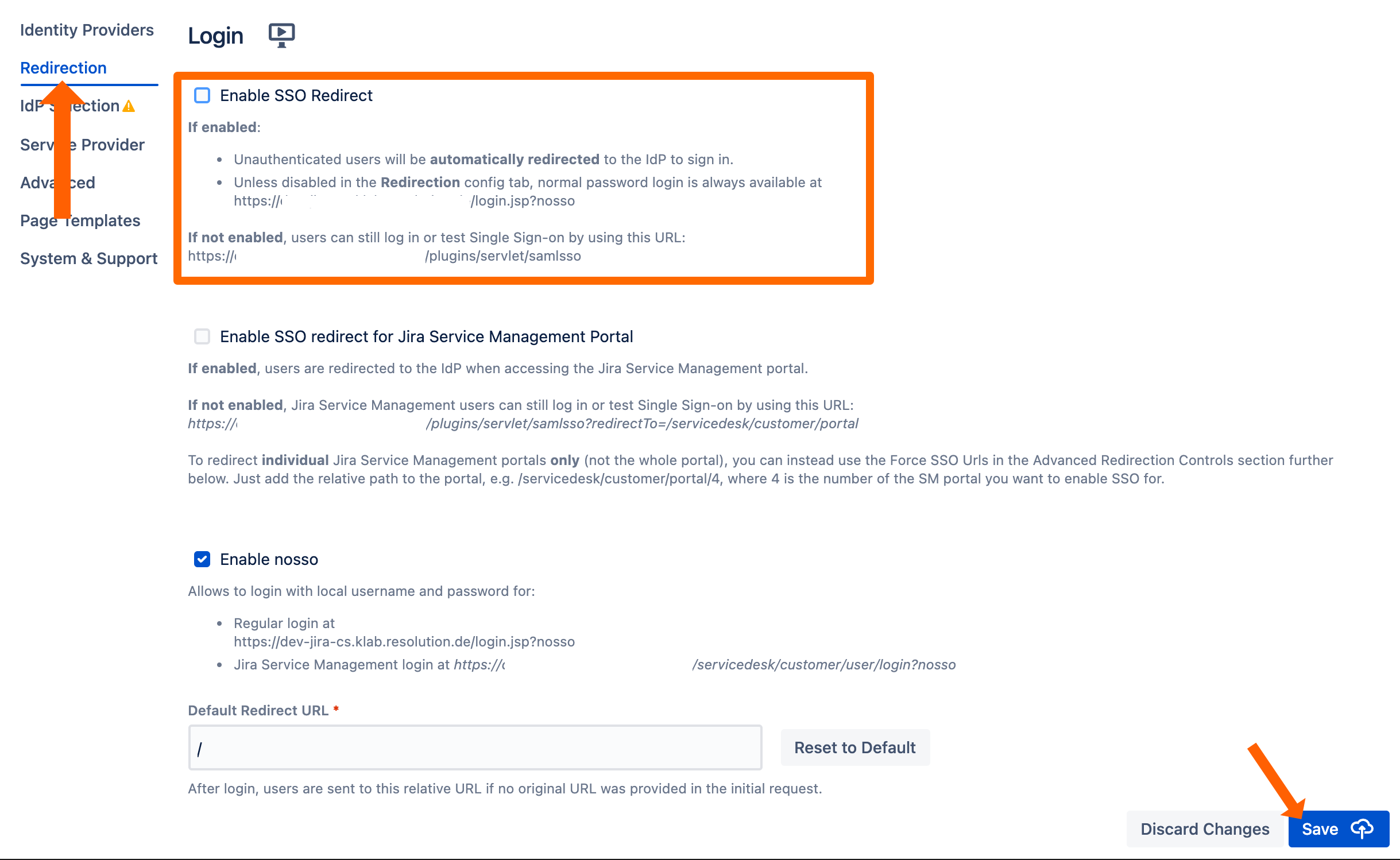
If Enable SSO Redirect is enabled, you can log in to your Atlassian application manually by browsing to the URL that matches your Atlassian application as listed below.
Use this URL, if you need to log in as a local user unknown to Okta or if there are any issues with Single Sign-On.
Jira: https://<baseurl>/login.jsp?nosso
Confluence: https://<baseurl>/login.action?nosso
Bitbucket: https://<baseurl>/login?nosso
Bamboo 5: https://<baseurl>/userlogin!default.action?nosso
Bamboo 6: https://<baseurl>/userlogin!doDefault.action?nosso
Read more about nosso here: https://wiki.resolution.de/doc/saml-sso/latest/jira/further-configuration/disable-password-login-with-nosso-parameter-v2-1-0
