Okta with Manual Provisioning
Goal
Configure SAML Single Sign-On for Atlassian Data Center / Server to work with Okta and manual provisioning.
Prerequisites
Okta Directory
Your Atlassian Data Center / Server application must be accessible via HTTPS. (read more about it in the Atlassian documentation, i.e. for Jira or Confluence)
Video Guide
The video below is an installation guide for setting up our SAML SSO app with Okta (watch on YouTube).
Step-by-Step Setup Guide
Find below a detailed guide on how to complete the setup of the SAML Single Sign On app with Okta and manual user provisioning,
meaning that users from Okta have to exist in your Atlassian application already.
If you need any further support, please feel free to contact us here.
Install the SAML SSO app
In your Atlassian product, open the in-product marketplace as described in the Atlassian documentation.
Search for "resolution saml" and click "Install" for SAML Single Sign On (SSO) by resolution Reichert Network Solutions GmbH.
After the installation is complete, click on Manage, then choose Configure.
Now, you are on the Add-on / app configuration page and the first step of the setup wizard will appear.
Configure SAML SSO app
To start the wizard and to configure Okta as your new identity provider, navigate to the administration console and search for SAML Single Sign On here:
Confluence: Confluence Administration/ General Configuration, search for USERS & SECURITY
Jira: User management tab
Bitbucket: Administration/ Accounts
Bamboo: Administration/ Security
Fisheye/ Crucible: Administration/ Security Settings
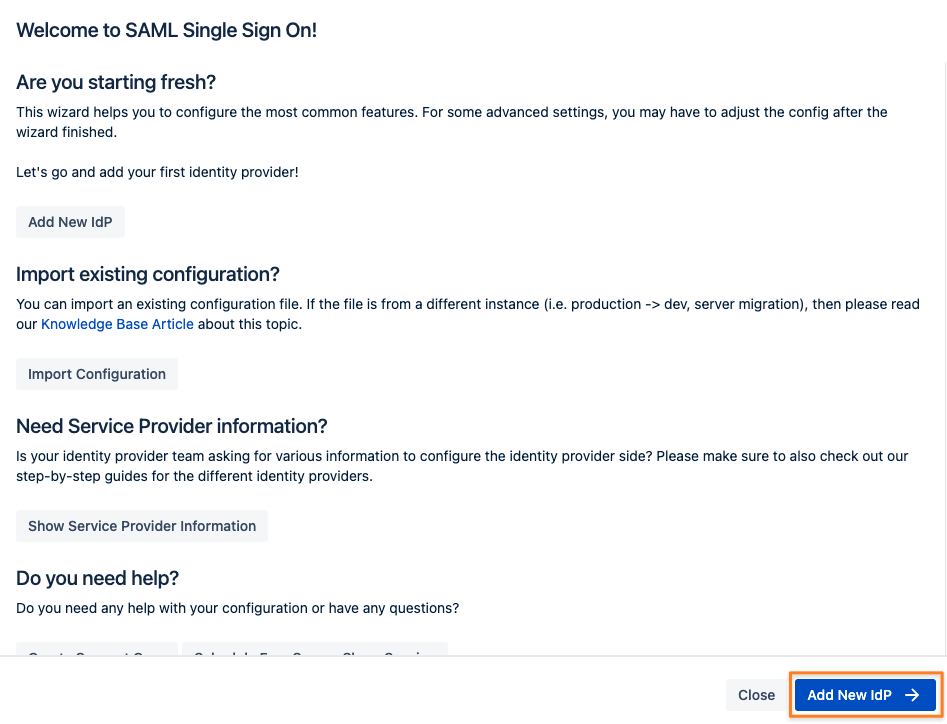
Click on it and the wizard start page will show.
Add new Identity Provider (IdP)
Click on Add new IdP to start the wizard.
Adding a new IdP can also be done without the wizard in the app configuration section Identity Providers/ Add new IdP
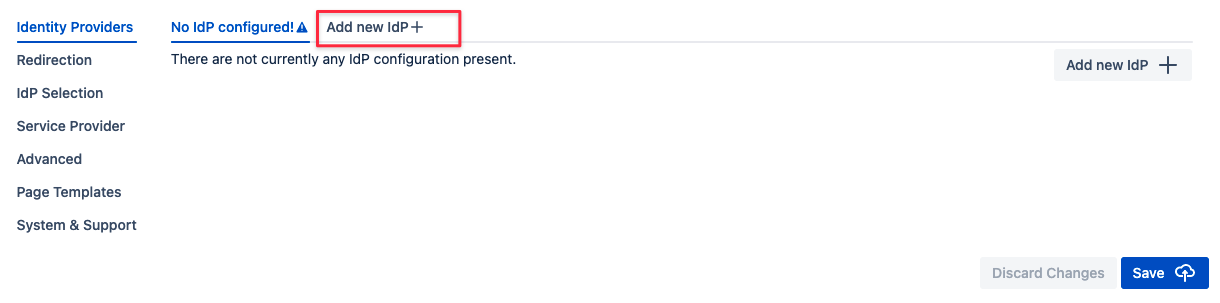
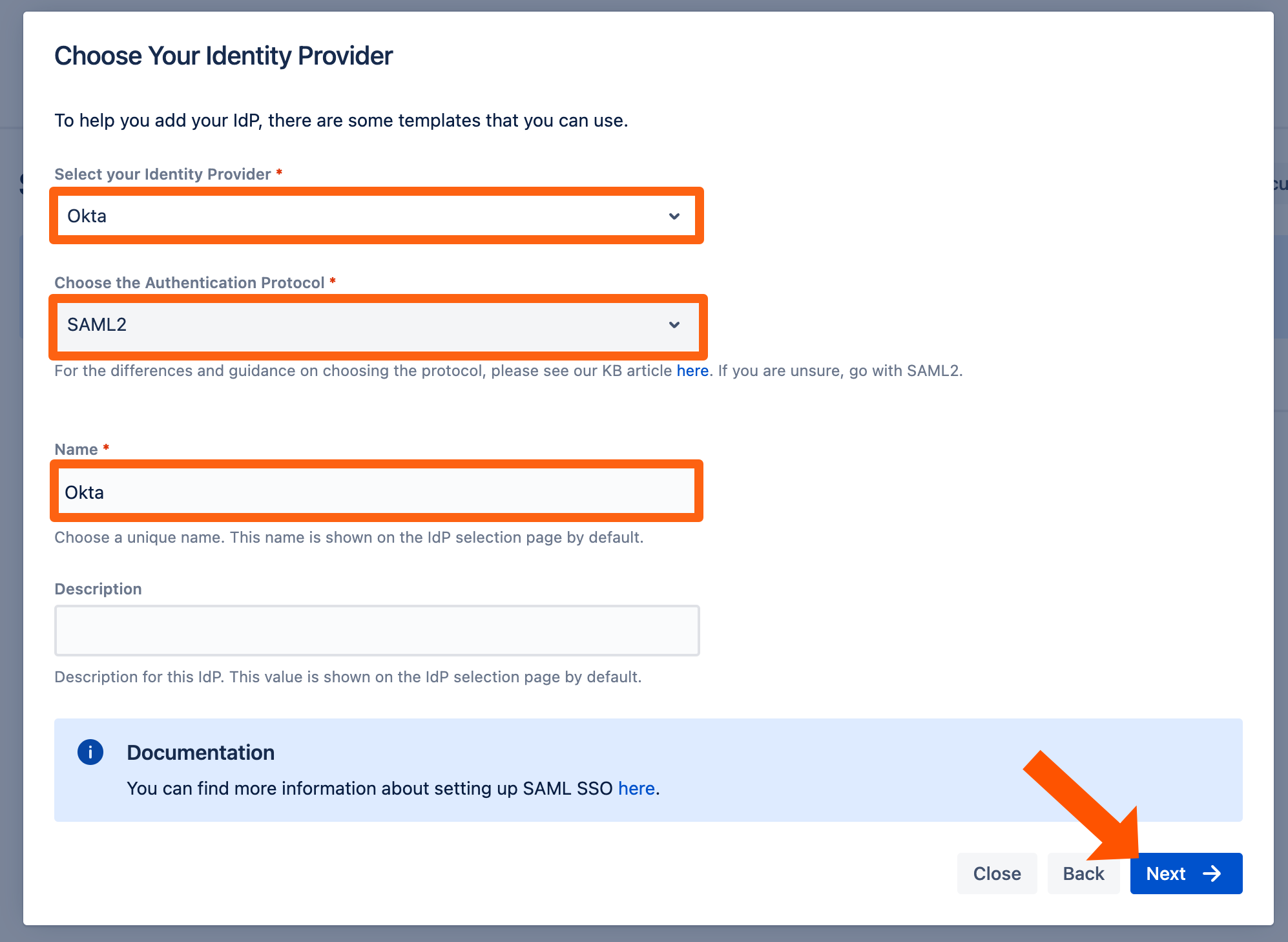
Select Okta as IdP Type.
You may also change the name and add a description. The name needs to be unique.
Keep the Authentication Protocol set to SAML2.
Click on Next.
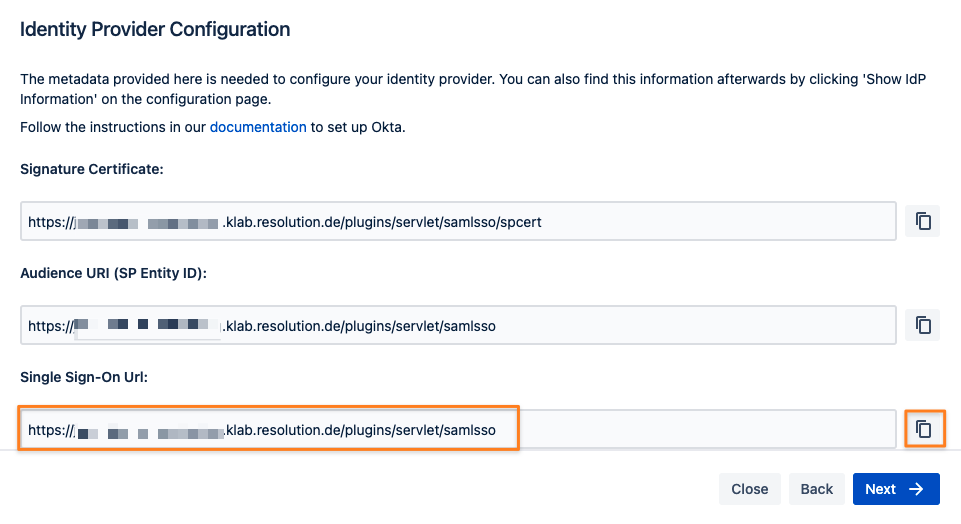
Retrieve SAML Metadata for Okta
Copy the Single sign-on URL from the screen, you'll need it in your Okta configuration web console.
Click on Next and leave that next screen as it is for now since we'll continue the setup in Okta.
Configure Okta
Now it's time to head over to Okta. Make sure you're logged in as Admin.
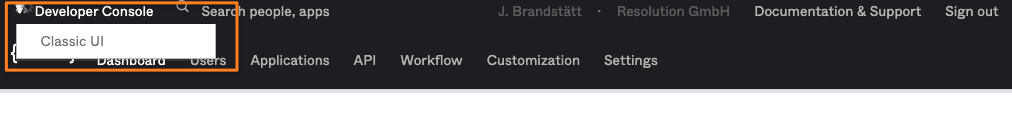
You need to switch to Developer Console/ Classic UI first, should you still see the black navigation bar:
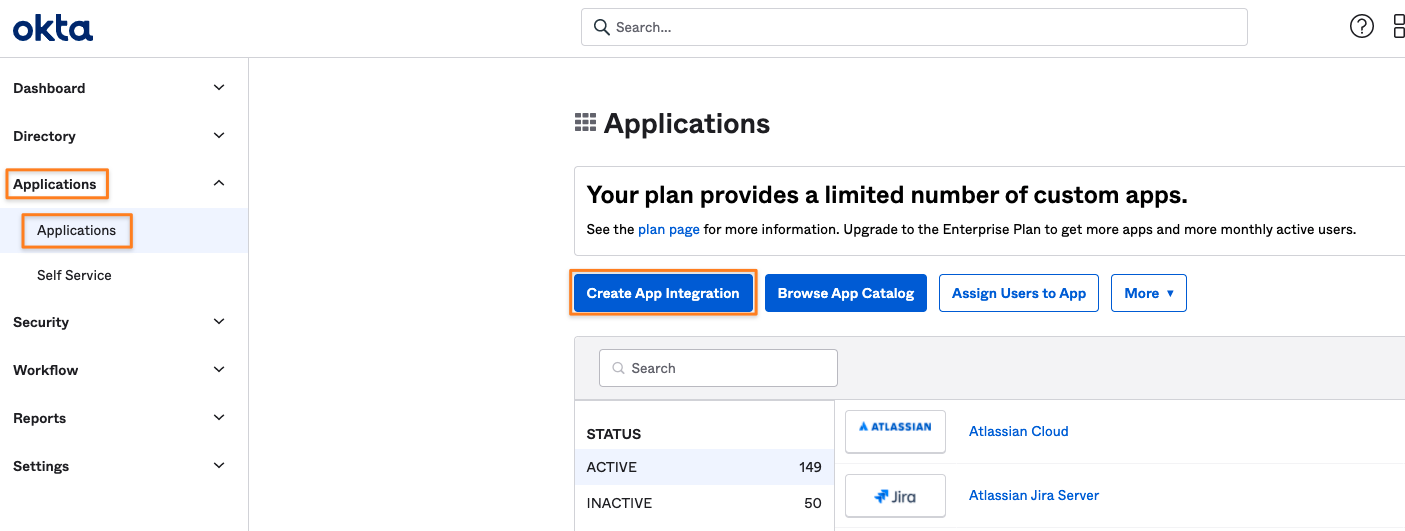
Once In classic mode, expand the Application menu on the left and click on Applications, and then the Create App Integration button:
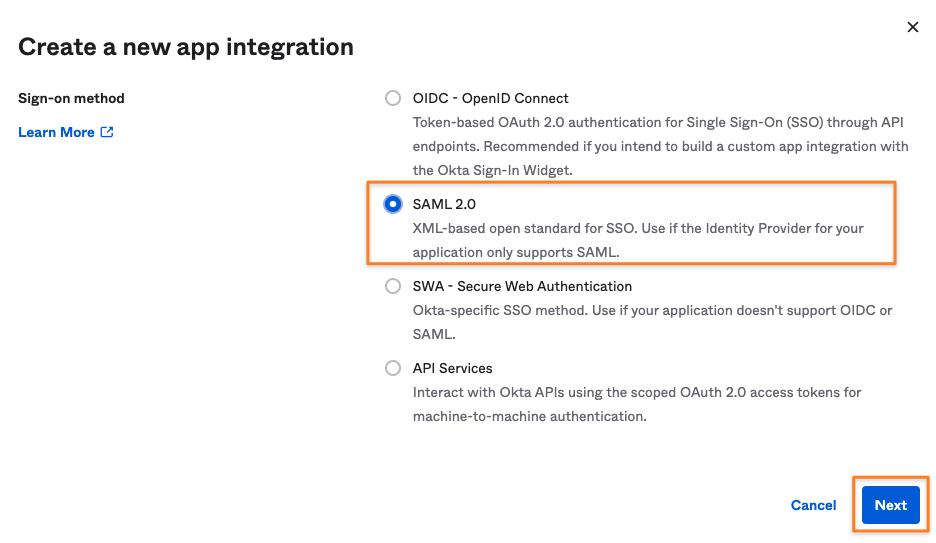
Select SAML 2.0 as the Sign-on method and click Next
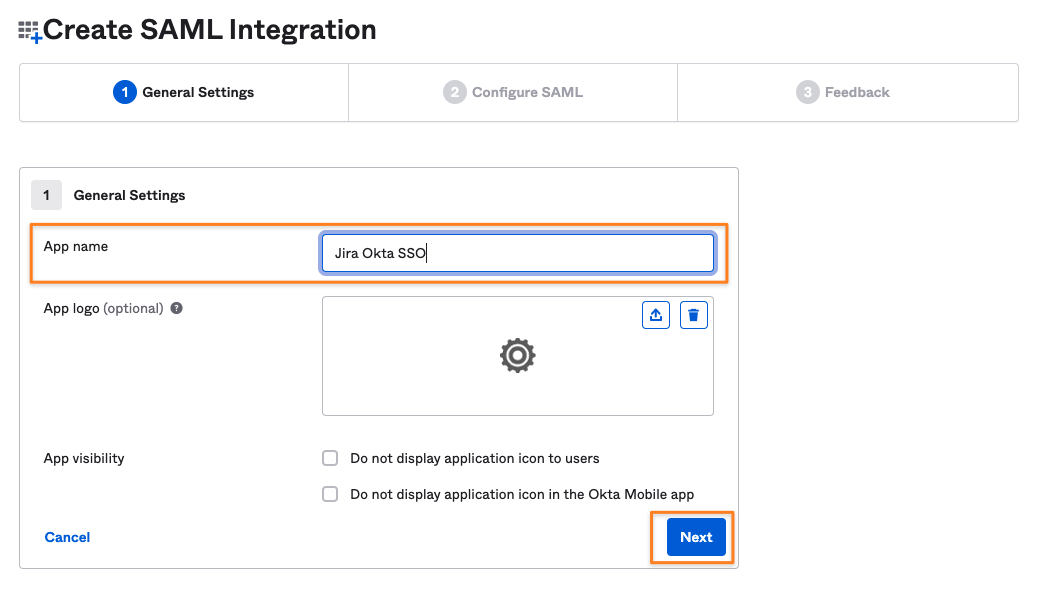
Provide an App name and click Next
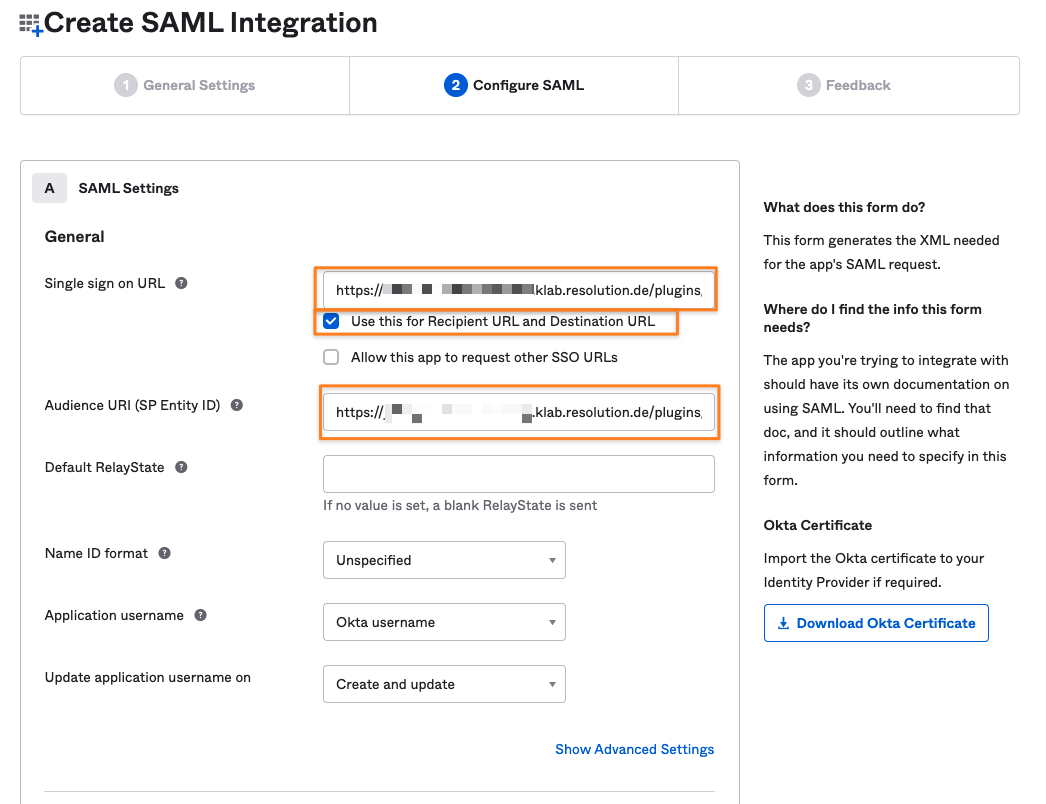
Paste the Single Sign-On URL to both the Single sign-on URL and the Audience URI (SP Entity ID) field.
Leave the Use this for Recipient URL and Destination URL checkbox enabled and click Next further down on the screen.
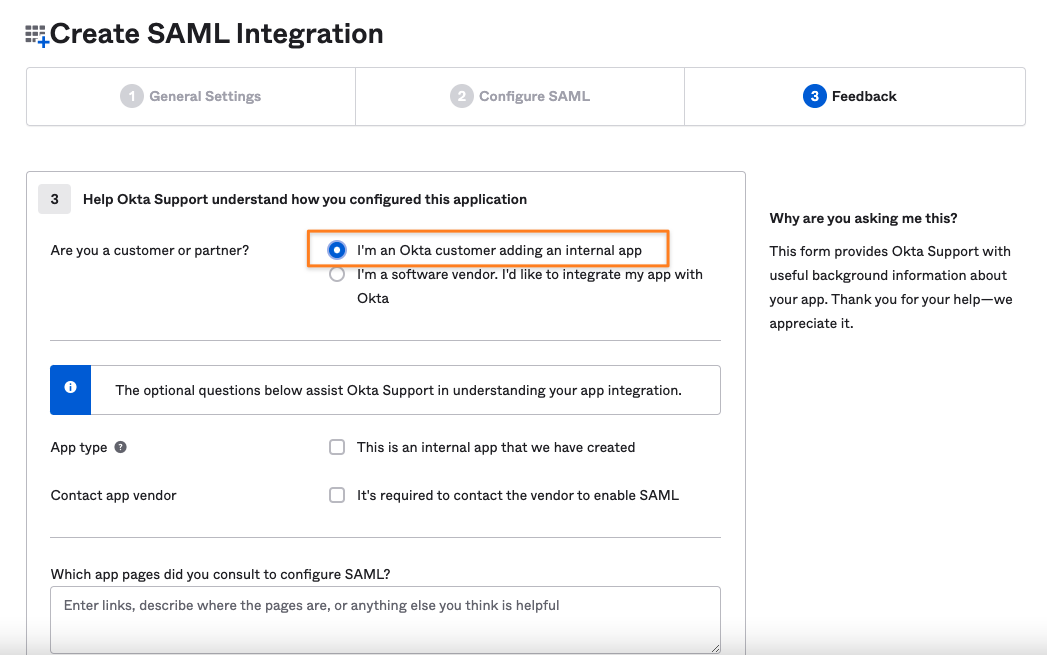
Step 3 is just for providing some feedback to Okta. Selecting I'm an Okta customer adding an internal app and clicking on Finish is all you need to do.
You'll be redirected to the Sign On tab from which you can get the Identity Provider metadata.
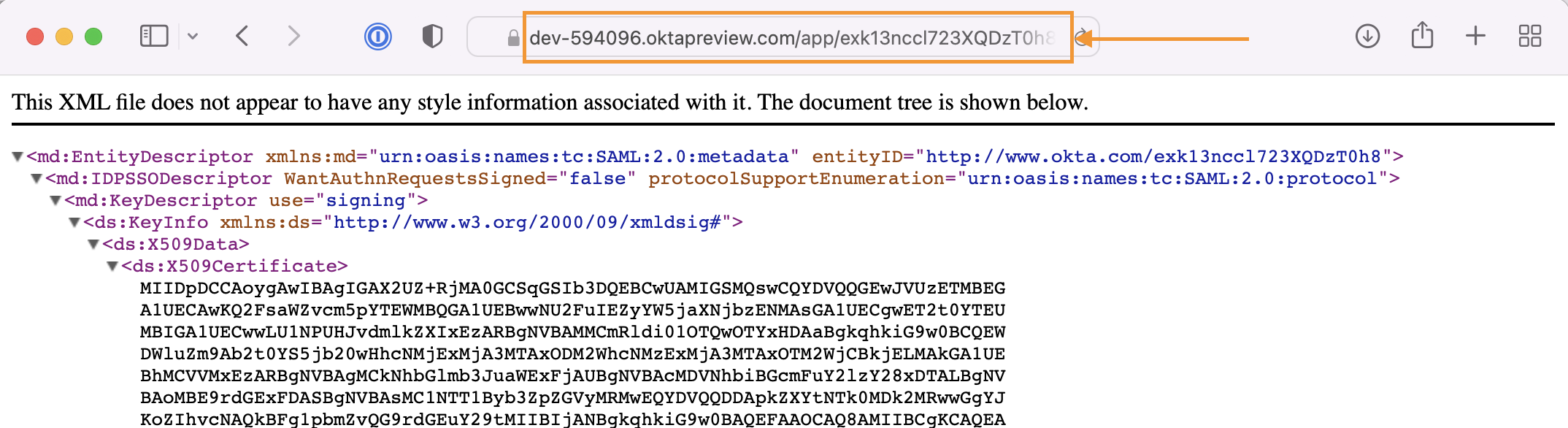
Under the SAML Signing Certificates section, click on Actions for the Active certificate, then choose View IdP metadata.
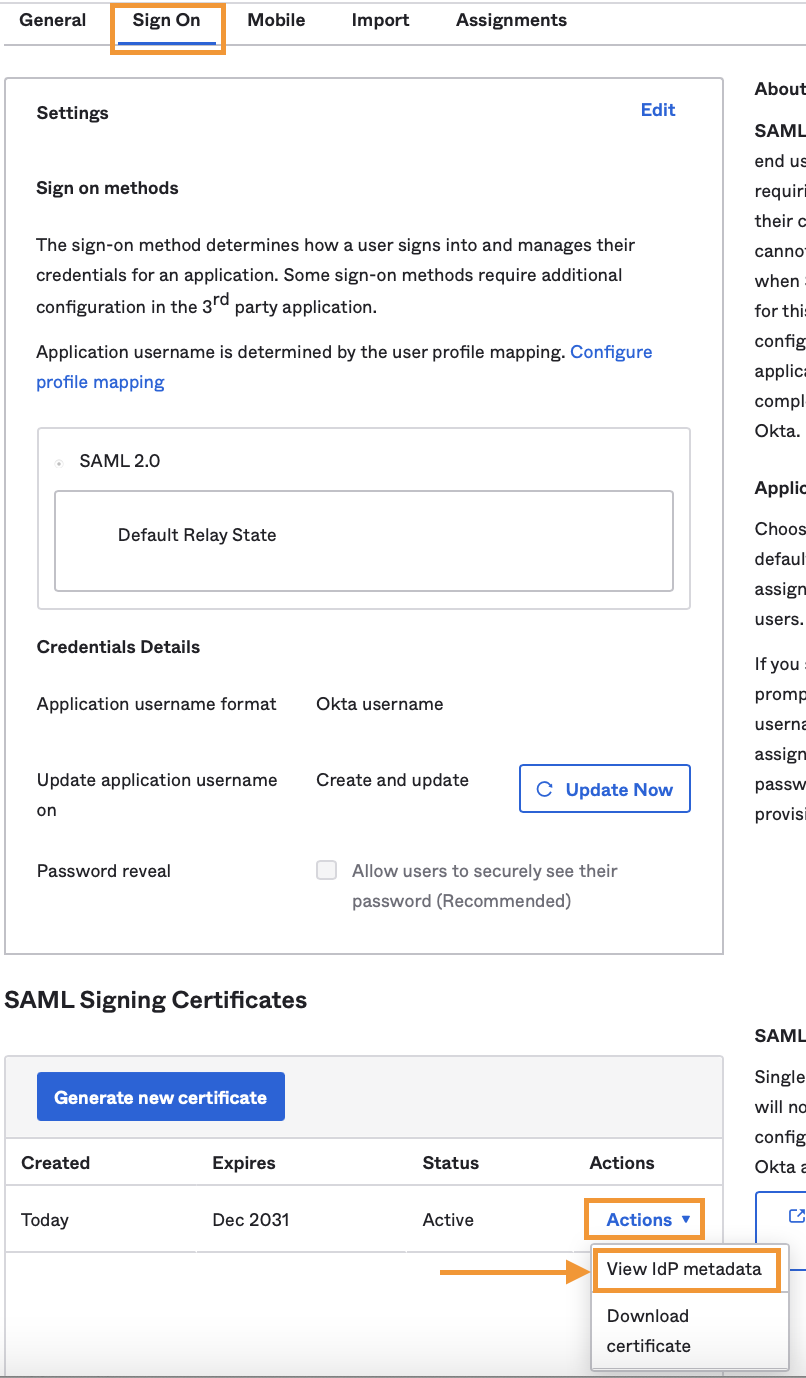
That would open a new page with the metadata XML, where you need to copy its URL from the address bar.
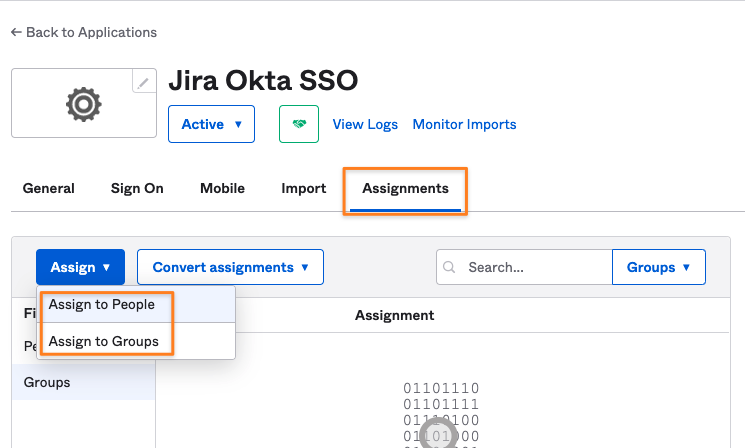
You also need to define which users and/ or groups should be allowed to sign in via SAML SSO in Okta via the app you've created.
Switch to the Assignment tab and use either the Assign to People or Assign to Groups button to define who should sign in with SSO.
Import SAML IdP Metadata
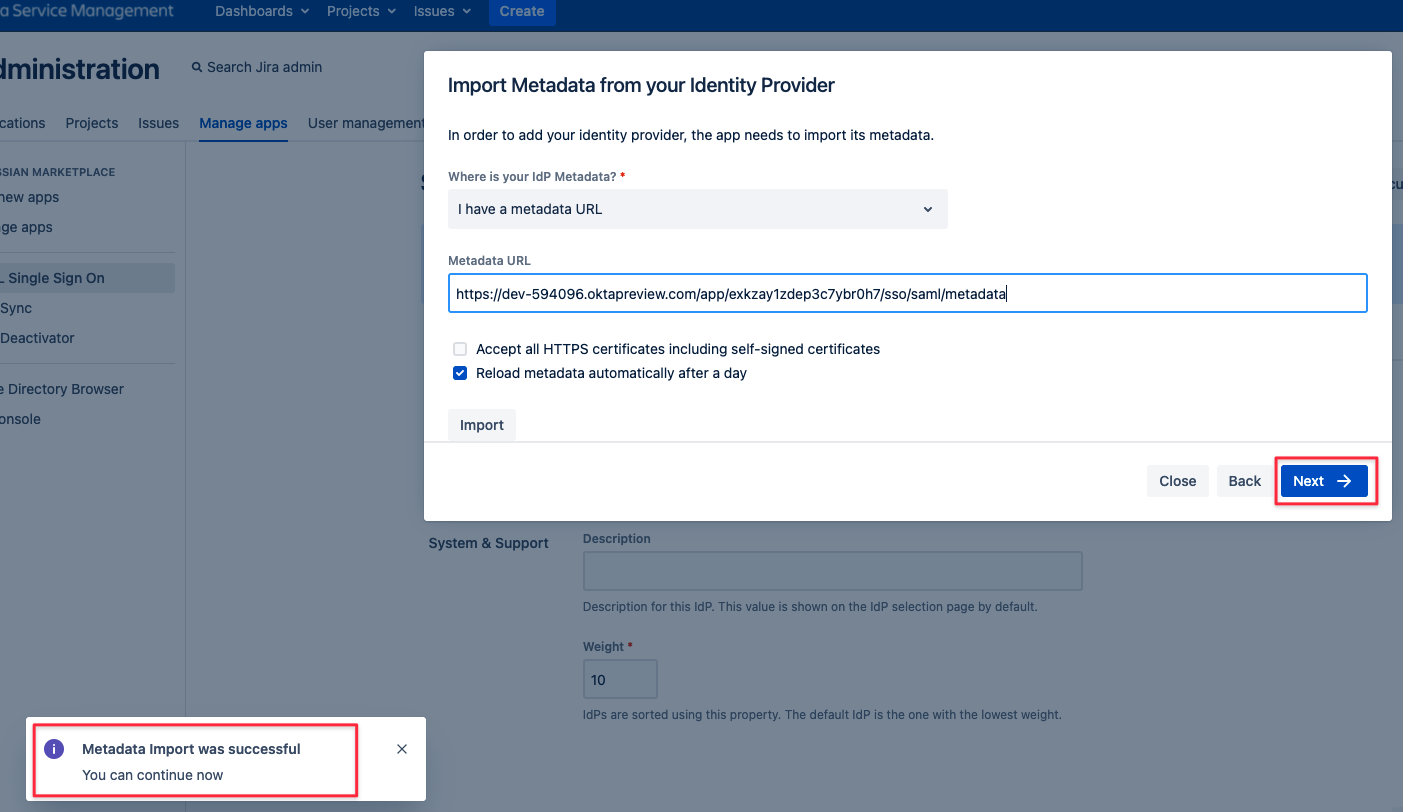
It's time to resume configuration on the SAML SSO side. Take the Okta metadata link you've copied
and paste it to the Metadata URL field in the corresponding field of the Import SAML IdP Metadata wizard screen still open.
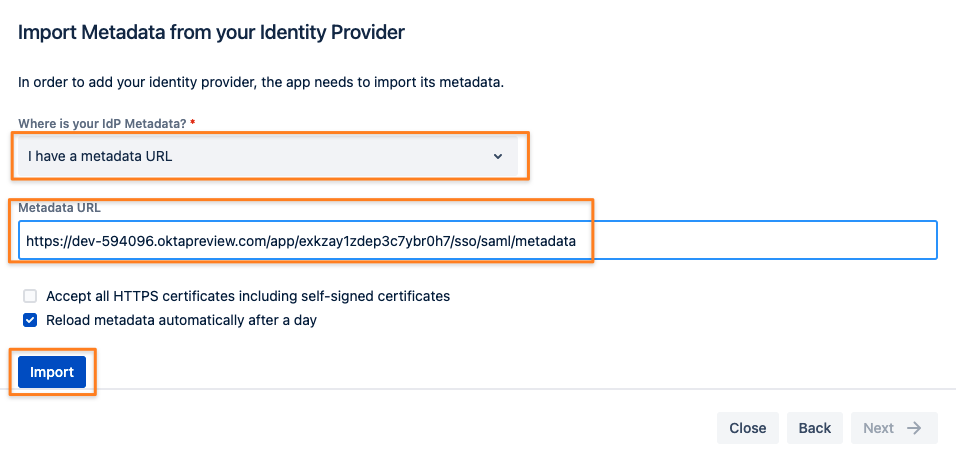
If loading the metadata from the URL worked, you can click Next
If it didn't work, your Atlassian instance can't talk directly to Okta (i.e. because traffic is blocked).
While you could also download the metadata first and import it manually by changing the Where is your IdP Metadata option,
we recommend making it work via URL. Our app supports automatic metadata refresh so that changes on the IdP will be reflected automatically after some time.
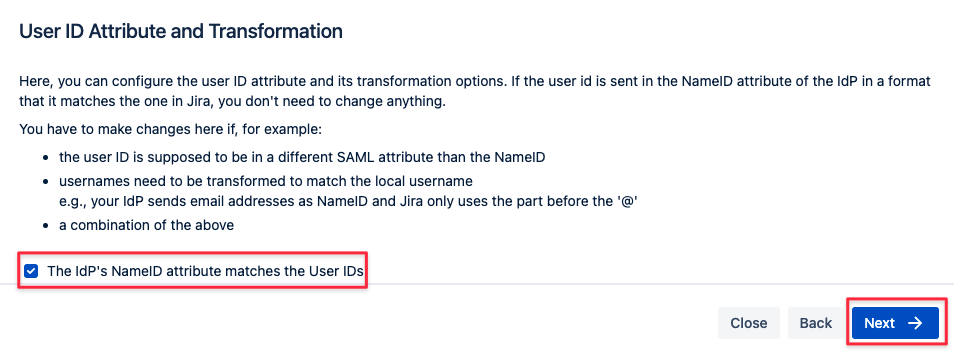
User ID attribute and transformation
It's recommended to leave this option checked. Click on Next.
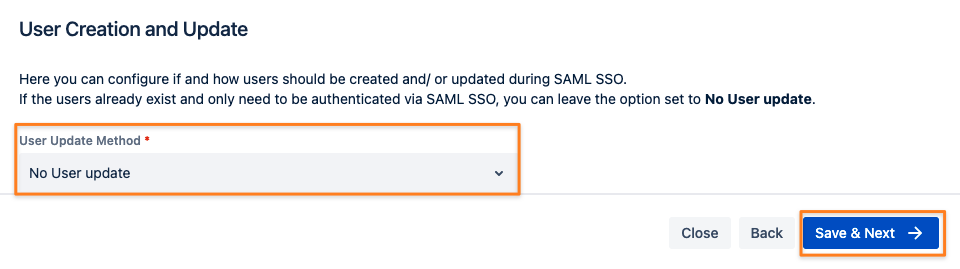
User creation and update
Unless you want to assign groups to users after authentication or planning to use just-in-time provisioning, you should
leave this option unchecked. This can be configured later anytime and is also subject of the Okta with Just-In-Time Provisioning tutorial
Click Save & Next to proceed.
Test configuration of SAML SSO app
The last step of the configuration wizard is a test that can be executed with the Start button.
Please remember that ...
the user you are testing with needs to be assigned to the SSO app you've just created in Okta as described earlier
the user also needs to exist in your Atlassian application already since we are not using just-in-time provisioning here
(part of the Okta with Just-In-Time Provisioning tutorial)
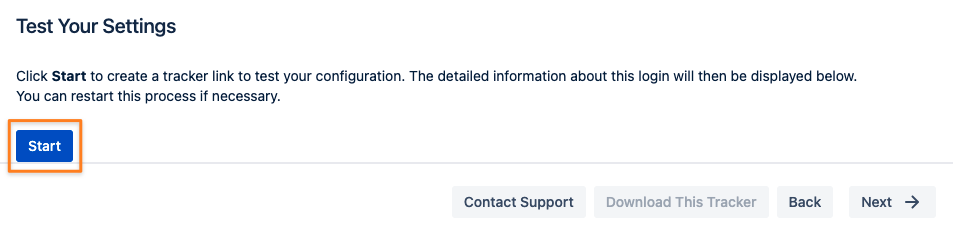
Copy the link displayed and paste it into a new incognito/ private browsing window, to execute a login with Okta.
The status of the authentication process is permanently updated in the window.
If successful, you should click Next
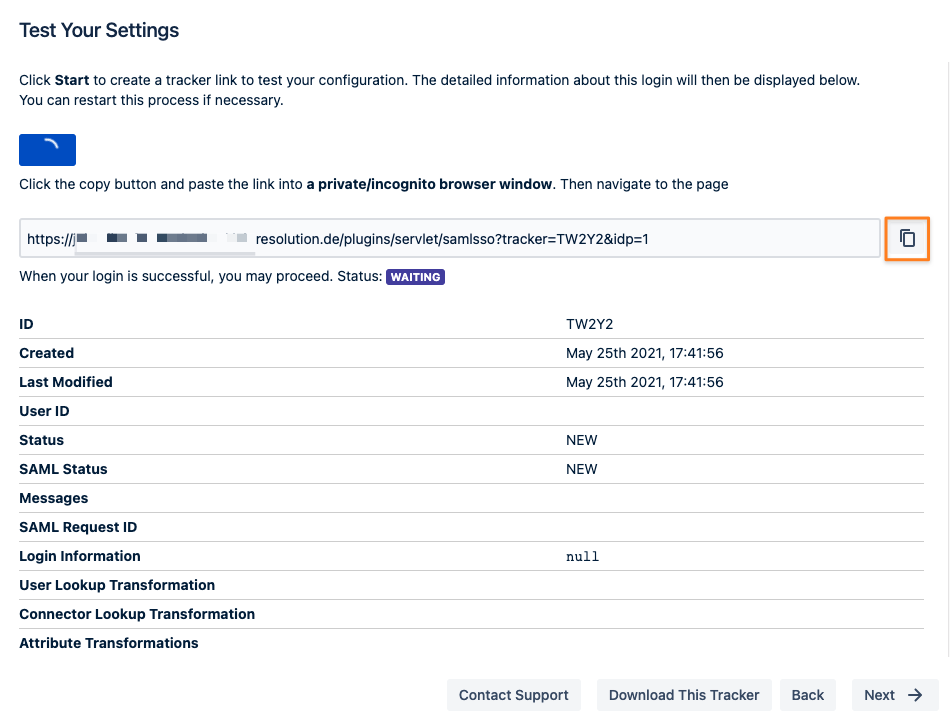
If there is any error at this point you need help with, please refer to the troubleshooting guide, which will also help us, should you open a support ticket with us.
Of course, the test window above will display a lot of information about the errors already.
Enable login redirection
The last step of adding Okta as your new IdP is to configure redirect options.
Selecting Enable SSO Redirect will ensure that users are getting redirected to be logged in via SAML,
instead of via the login form as before the SSO setup.
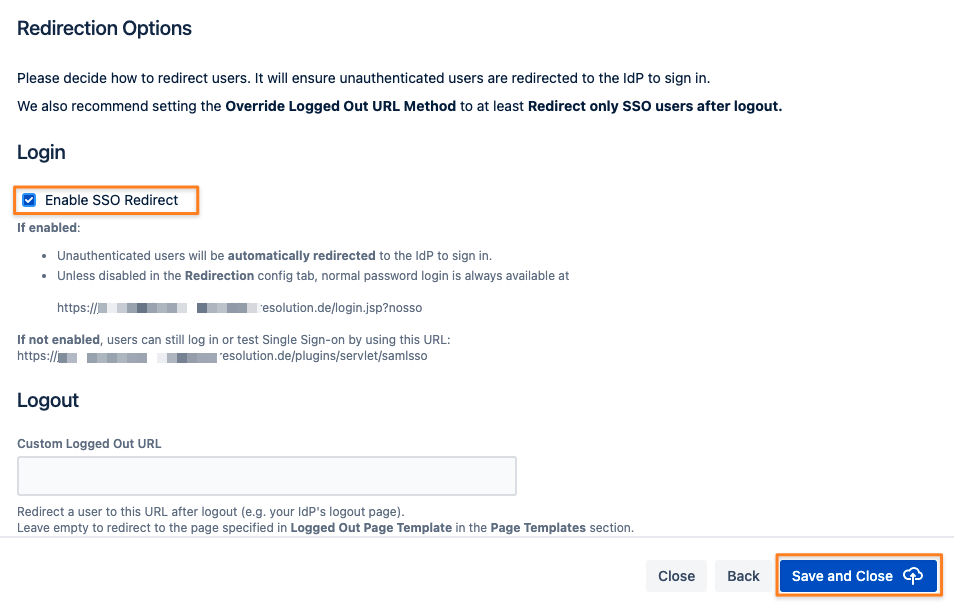
Complete the setup by clicking Save and Close
If Enable SSO Redirect is enabled, you can log in to your Atlassian application manually by browsing to the URL that matches your Atlassian application as listed below.
Use this URL, if you need to log in as a local user unknown to Okta or if there are any issues with Single Sign-On.
Jira: https://<baseurl>/login.jsp?nosso
Confluence: https://<baseurl>/login.action?nosso
Bitbucket: https://<baseurl>/login?nosso
Bamboo 5: https://<baseurl>/userlogin!default.action?nosso
Bamboo 6: https://<baseurl>/userlogin!doDefault.action?nosso
Read more about nosso here: https://wiki.resolution.de/doc/saml-sso/latest/jira/further-configuration/disable-password-login-with-nosso-parameter-v2-1-0
