GitHub with Manual Provisioning
Goal
After completing this setup guide, you will have set up GitHub with manual provisioning and your Atlassian product for the SAML SSO for Atlassian Server or Data Center app. Additionally, you will enable the SSO redirection and test SSO.
If you need help, please reach out to us at https://www.resolution.de/go/support. You can also book a free meeting via https://www.resolution.de/go/calendly.
Prerequisites
To use the SAML SSO app for Atlassian Server or Data Center with Azure AD, you need the following:
A GitHub Account
A (trial) subscription for the SAML SSO app
Admin access to your Atlassian product
Step-by-Step Setup Guide
Install the SAML SSO App
In your Atlassian product, open the in-product marketplace as described in the Atlassian documentation.
Search for "resolution saml" and click "Install" for SAML Single Sign On (SSO) by resolution Reichert Network Solutions GmbH.
After the installation is complete, click Manage Apps/Addons.
Configure SAML SSO
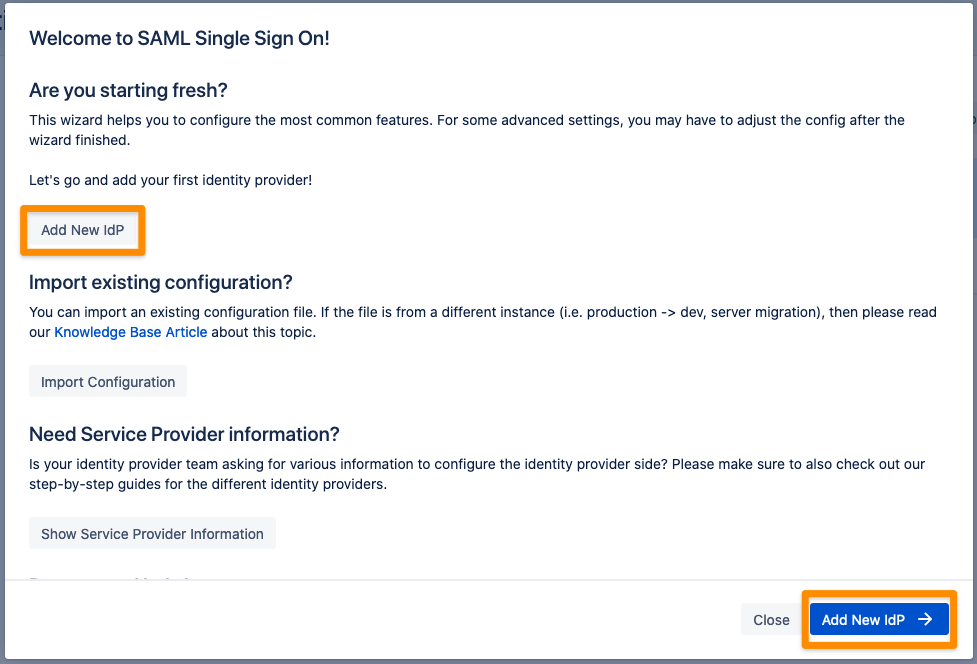
After you clicked "Configure", the Wizard will be triggered. If not, or if you want to add another Identity Prover (IdP) to your existing configuration, click on "+ Add IdP". This guide assumes, that there is no IdP configured.
The Wizard greets you with information, click on "Add new IdP" to proceed.
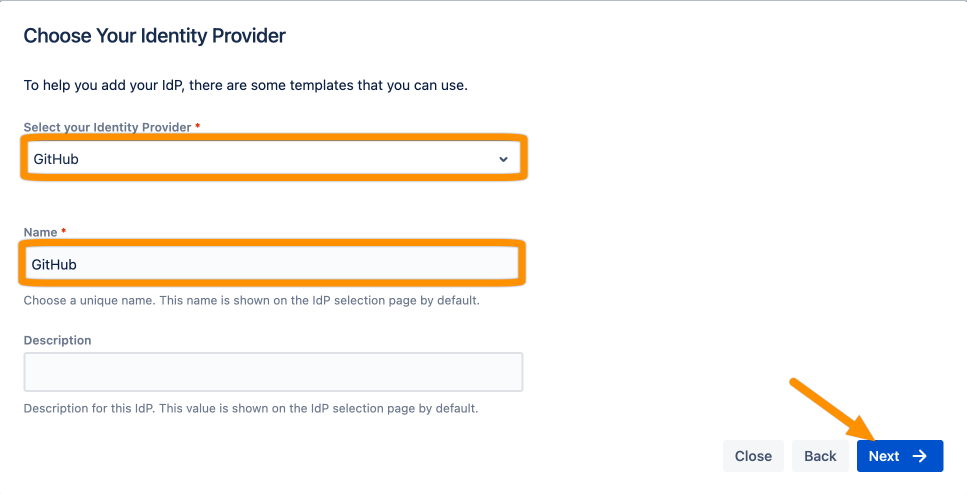
Choose GitHub for the identity provider and click Next.
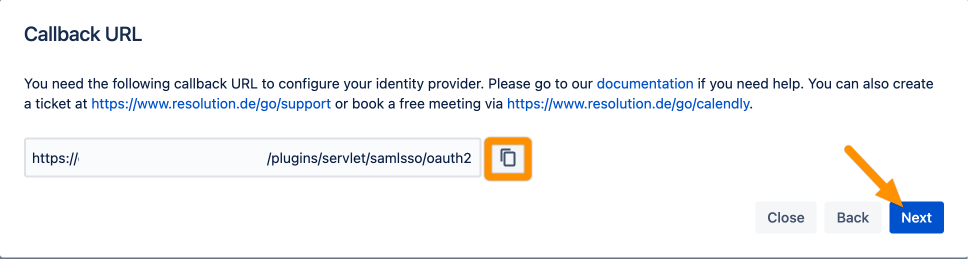
Copy the Callback URL and keep it ready for the next step. Click Next.
Go to this page to register a new application via GitHub. Enter your base URL for the Homepage URL and paste the Authorization callback URL from the previous wizard step. Click Register application to proceed.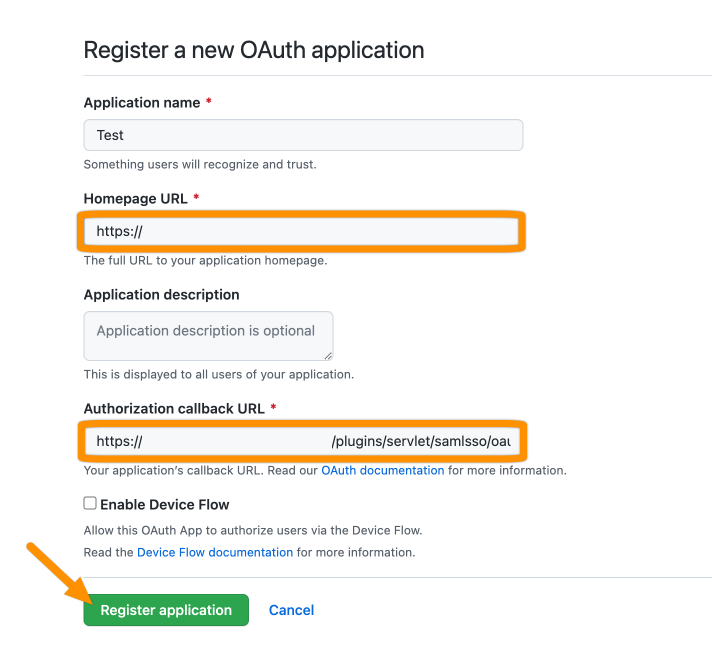
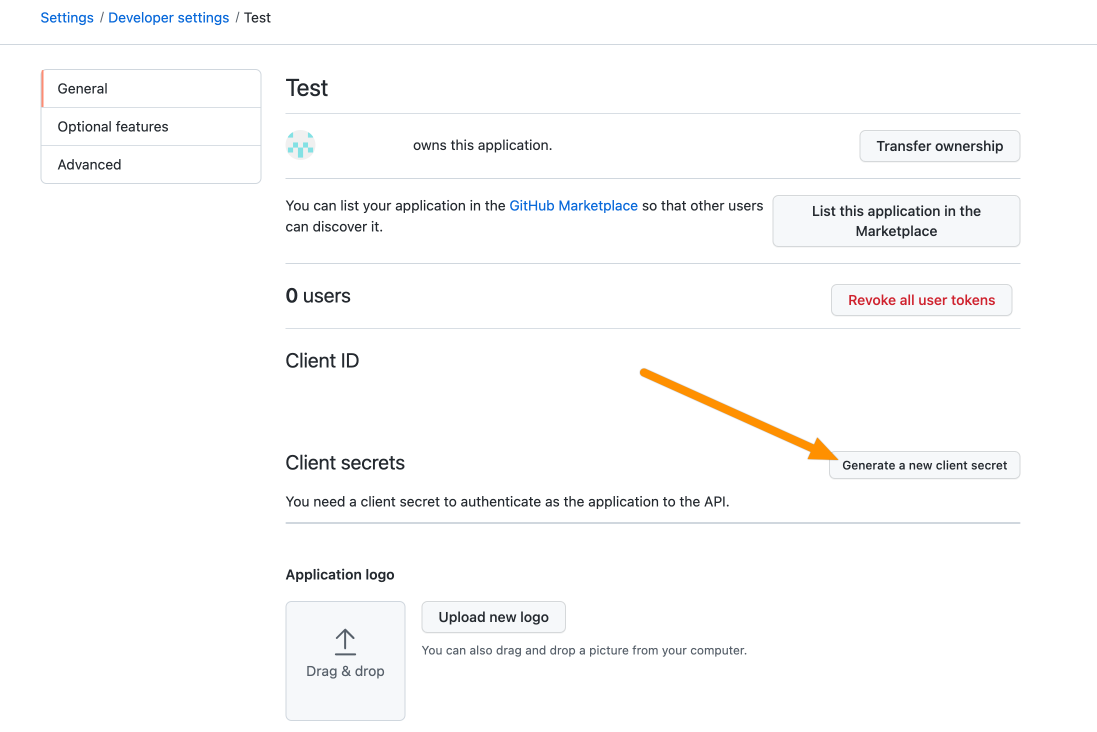
Click Generate a new client secret.
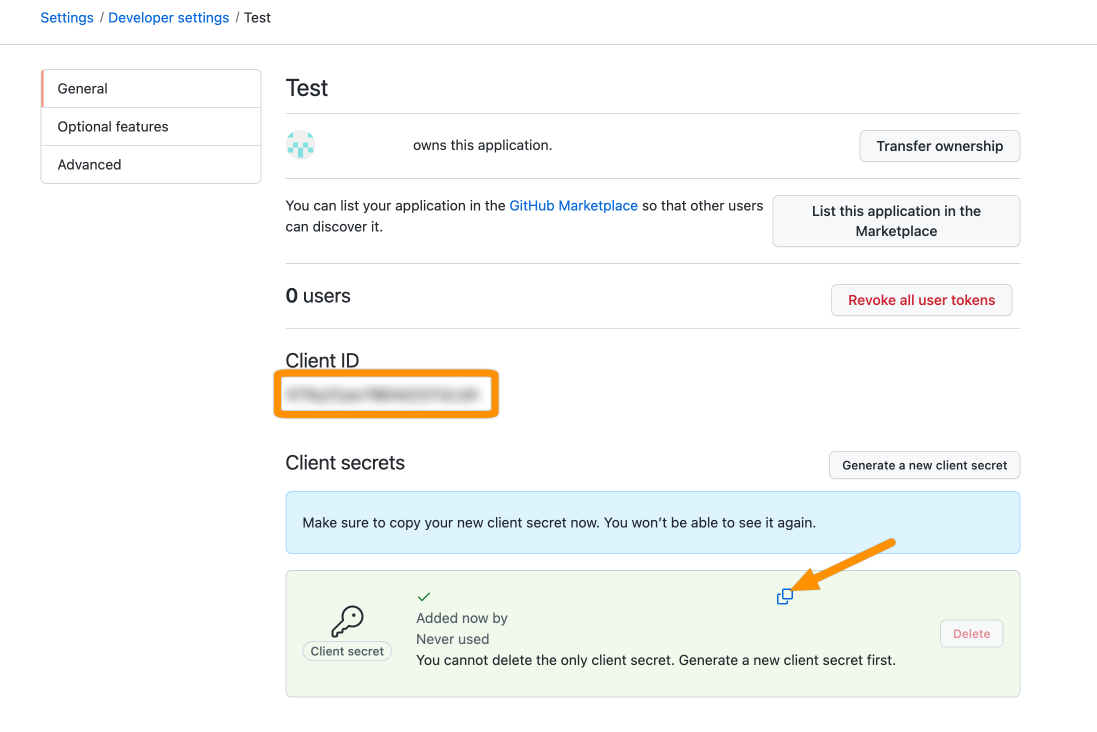
Copy the Client ID and the Client secret.
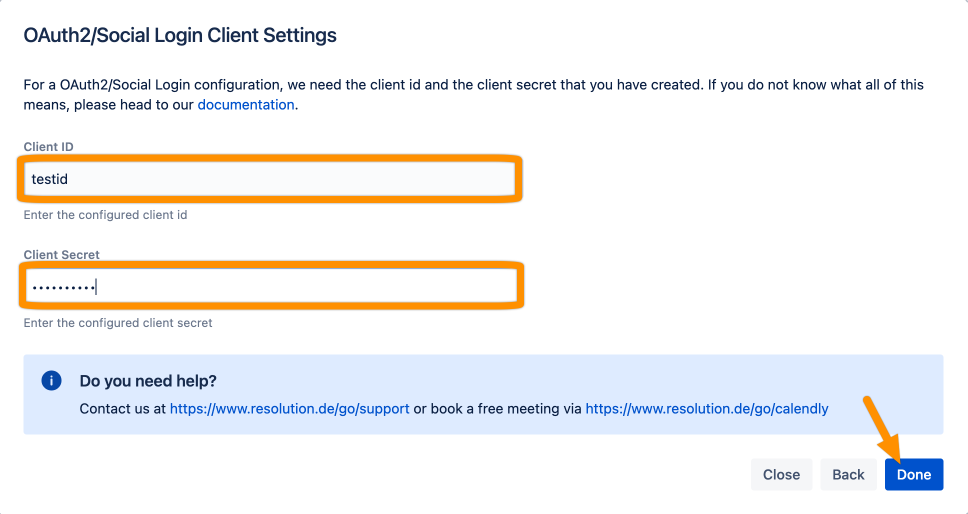
Add the Client ID and Client Secret. Click Done.
Click Save to save the configuration.
That's it!
